keycloak
Articles tagged with keycloak.

Okta vs Keycloak: Policies vs Authentication Flows Details
Compare Okta’s policy-based authentication with Keycloak’s flow-based model. Learn how MFA, fallback, and conditional access work in real-world IAM scenarios.

Keycloak 26.6+ Workflows: Automating Identity
Explore Keycloak 26.6 workflows to automate onboarding, enforce policies, and manage user lifecycle with simple YAML-based automation.
JWT Authorization Grant in Keycloak with Node.js
Learn how to implement JWT Authorization Grant in Keycloak 26.6 using a custom Node.js token issuer, including IDP setup, user…
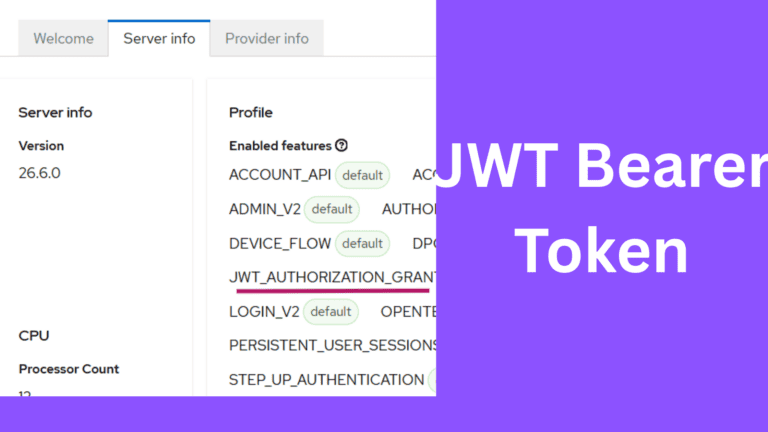
JWT Authorization Grant in Keycloak with External IdP
Learn how to implement JWT Authorization Grant in Keycloak using Auth0 as an external Identity Provider, including setup steps and…
Keycloak Realm Not Found: Causes and Solutions
Fix Keycloak realm not found errors. Covers common typos, case sensitivity, URL pattern changes, realm import failures, and version migration…
Clerk Alternatives in 2026: Why Developers Are Choosing Keycloak
Compare the best Clerk alternatives in 2026: Keycloak, Auth0, Stytch, Descope, and WorkOS. Detailed pricing, DX, enterprise features, and migration…
Keycloak Custom SPI Development: Build Your First Extension
Build custom Keycloak extensions using the SPI framework. Complete tutorial covering EventListenerProvider, Authenticator, and UserStorageProvider with code.
Keycloak Connection Refused: Troubleshooting Guide
Fix Keycloak connection refused errors. Covers port binding, Docker networking, health checks, database connectivity, hostname config, and proxy settings.

Keycloak vs Clerk: When to Choose Open Source Over Managed Auth
Compare Keycloak and Clerk for authentication. Explore developer experience, pricing at scale, enterprise features, customization, and data ownership.
Auth0 vs Keycloak: Login & Token Customization
Learn how Auth0 and Keycloak handle login control and token customization. Explore Actions, Authentication Flows, Protocol Mappers, and architecture trade-offs.
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.