What to Do With the Default Clients in Your Newly Created Keycloak Realm?
Last updated: March 2026
Introduction to Default Clients
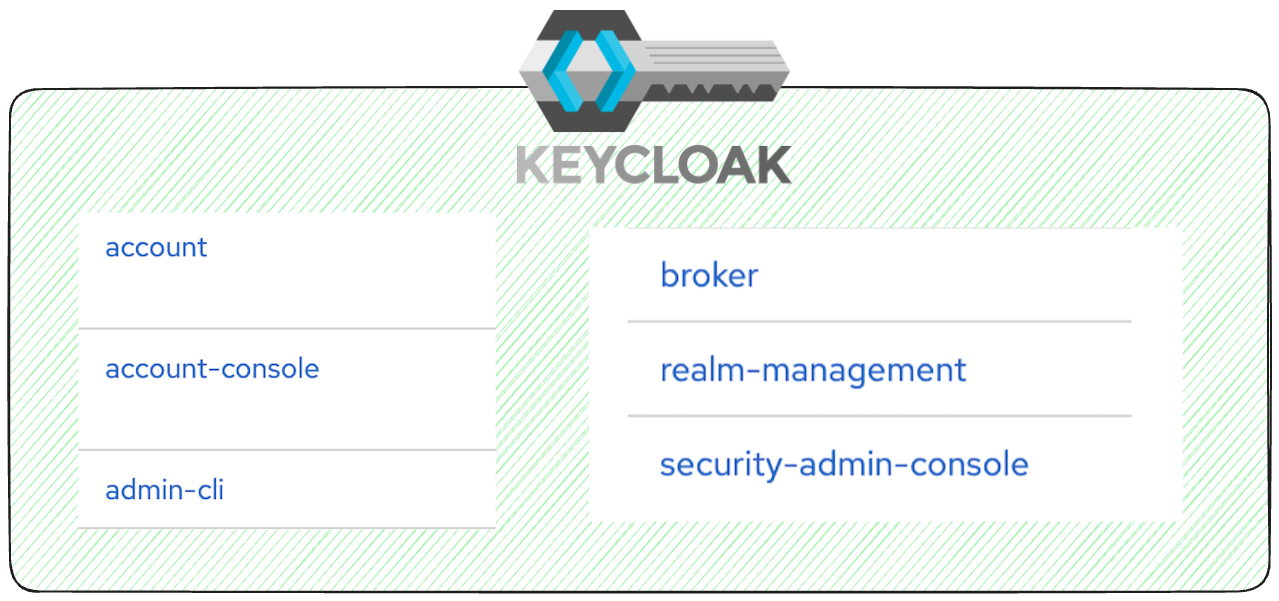
When you create a new Keycloak realm, several default clients are automatically generated. These clients enable core functionalities for managing users, realms, and external identity providers. Understanding and properly configuring these clients is critical for a secure Keycloak deployment. Here’s a breakdown:
- account: Represents the backend for the account API, containing roles for managing user accounts. It is configured as an OIDC confidential client. See the Keycloak Account Service documentation for details.
- account-console: Provides a frontend for user account management. This is an OIDC public client tailored for single-page applications. See the Account Console documentation.
- admin-cli: Used for managing realms via CLI tools like
kcadm.sh. For automated realm provisioning, a custom client using only client credentials is often preferred. See the Admin CLI documentation. - broker: Serves as the backend for identity brokering. For better control over redirect URIs, scopes, and mappings, dedicated backends for specific identity providers are recommended. See the Identity Brokering documentation.
- security-admin-console: Manages the admin UI for a specific realm. If scoped to a non-master realm, it limits administrative capabilities to that realm only. See the Admin Console documentation.
- realm-management: Provides the backend API for realm-specific management roles. This client does not exist in the master realm but is available for other realms. See the Realm Roles documentation.
Step 1: Audit and Understand Each Client
Understanding the purpose and configuration of each default client is crucial. Use the Admin Console to:
- Examine each client’s roles, settings, and scopes.
- Ensure that redirect URIs and protocol mappings are appropriate for your setup.
For a broader look at initial Keycloak setup best practices, read our guide on 8 default configurations to adjust right away on your Keycloak cluster.
Step 2: Harden Security for Critical Clients
- account & account-console: Restrict user roles to authenticated accounts. Enhance security by enabling passwordless authentication using WebAuthn or passkeys.
- admin-cli: Limit access to specific administrators. For automated tasks, consider using a custom client configured for client credentials only. Security tip: Disable this client entirely if you do not use CLI-based administration, as it reduces your attack surface.
- broker: Define strict redirect URIs, scopes, and protocol mappings to secure interactions with external identity providers. Security tip: If you are not using identity brokering, disable this client to prevent unauthorized federation attempts.
- security-admin-console: Enforce two-factor authentication (2FA) and regularly monitor admin access logs. Consider using audit logs to track admin actions.
- realm-management: Ensure only necessary roles are granted to users. Regularly review permissions and scopes. Security tip: Audit the default scopes assigned to this client and remove any that are not required for your use case.
Step 3: Manage Realm-Specific Clients
In addition to the default clients, Keycloak generates realm-specific management clients in the master realm. For example, if you have a realm named new-realm, the master realm will include a client named new-realm-realm. These clients allow administrators in the master realm to manage the new-realm realm with dedicated roles.
Ensure these clients are properly configured with specific permissions to prevent unauthorized access.
Step 4: Minimize Attack Surface
- Disable unused clients to reduce potential vulnerabilities. Any default client that your deployment does not actively use should be disabled rather than left in its default enabled state.
- Use specific redirect URIs to avoid open redirects and misuse.
- Limit token scopes to adhere to the principle of least privilege.
- Review default scopes: Each client comes with default scopes that may grant more access than necessary. Navigate to each client’s “Client scopes” tab and remove any scopes that are not required.
Step 5: Implement Best Practices
Enhance your realm’s security by:
- Rotating cryptographic keys regularly to secure tokens.
- Enforcing HTTPS for all communications.
- Enabling audit logging to monitor and review user and admin activities.
- Configuring single sign-on (SSO) policies that align with your organization’s security requirements.
For a deeper look at Keycloak security best practices, visit the Skycloak documentation.
Step 6: Test Your Setup
Simulate common user and admin flows to validate your configurations. Monitor logs for errors or suspicious activities.
Conclusion
While default clients provide a strong foundation for managing Keycloak, thoughtful configuration is essential to ensure security and operational efficiency. Regularly review and update their settings, enforce strict access controls, and disable unused clients. For a managed Keycloak experience where these hardening steps are handled for you, explore Skycloak hosting.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.

