Authentication Technology Refresh: Modernization Planning and Timeline
Last updated: March 2026
Organizations are under increasing pressure to update outdated authentication systems due to evolving security threats, compliance requirements, and the demands of remote work. This article explores why legacy systems fall short and how modern authentication solutions address these gaps through stronger security, improved user experiences, and better scalability. It also provides a step-by-step guide to evaluate, plan, and execute a successful migration, including recommendations for choosing the right protocols and deployment models.
Key takeaways:
- Why Modernize? Legacy systems struggle with advanced security threats, compliance mandates like SOC 2 and HIPAA, and the flexibility needed for remote work.
- Modern Authentication Benefits: Protocols like OIDC, SAML, OAuth2, and WebAuthn enable passwordless flows, Single Sign-On (SSO), and adaptive Multi-Factor Authentication (MFA).
- Migration Strategy: Includes system audits, pilot testing, phased rollouts, and decommissioning legacy systems.
- Deployment Options: Self-hosted, managed cloud, or hybrid models, each with distinct trade-offs in control, cost, and complexity.
- Security and Compliance: Emphasize adaptive MFA, centralized role-based access, and alignment with frameworks like NIST, GDPR, and HIPAA.
This guide offers practical insights into navigating the challenges of authentication modernization while maintaining security, compliance, and operational continuity.
Reviewing Your Current Authentication Setup
When it comes to modernizing outdated systems, the first step is to take a hard look at your current authentication setup. This review isn’t just about identifying what’s broken — it’s about uncovering hidden dependencies, security weaknesses, and technical debt that could derail your timeline or inflate your budget.
Checking Your Current Systems
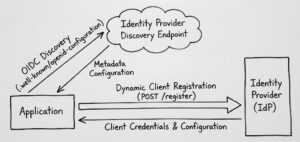
Start by cataloging every point where authentication occurs. This includes primary systems like Active Directory or LDAP, as well as application-specific logins. Map out how users interact with these systems, and note which endpoints rely on modern protocols like SAML or OIDC versus older methods such as NTLM or basic authentication.
Take a close look at your security posture. Are password policies strong enough? Do you have multi-factor authentication in place? Evaluate session management, access controls, and encryption standards.
Another critical area to examine is system performance and integration capabilities. Legacy systems often struggle with high user loads, slow response times, or limited compatibility with modern tools.
Finding Migration Problems
One of the most common hurdles in modernization projects is legacy directory dependencies. Applications that directly query LDAP or rely on custom Active Directory schema extensions may need significant rework.
Another issue is hardcoded configurations. These can be hidden in application scripts, infrastructure components, or configuration files. Look for hardcoded server names, IP addresses, or authentication endpoints that could break during the transition.
Don’t overlook compliance and audit requirements. These often dictate specific authentication methods, data retention policies, or session management rules.
Lastly, consider skills and resource gaps. Does your team have experience with modern authentication protocols or cloud identity services?
Migration Readiness Checklist
- Technical Readiness: Ensure your network supports modern protocols like SSL/TLS and confirm that backup and recovery procedures are solid.
- Application Compatibility: Create a detailed inventory of applications that depend on authentication. Prioritize applications based on their business importance and technical complexity.
- User Impact Assessment: Identify which user groups will experience the most significant changes.
- Compliance Alignment: Review your compliance posture to identify gaps that your modernization effort should address.
- Budget and Timeline Validation: Account for costs like software licenses, professional services, staff training, and potential application updates.
- Risk Mitigation Planning: Develop rollback procedures for each phase of the migration.
Choosing Modern Authentication Protocols and Systems
Authentication Protocols: OIDC, SAML, OAuth2, and WebAuthn
| Protocol | Best For | Key Strengths | Main Limitations |
|---|---|---|---|
| OIDC | Modern web/mobile apps, cloud integration | Simplified JSON format, strong mobile support, built-in identity claims | Requires technical expertise; limited legacy support |
| SAML | Enterprise federation, legacy system integration | Well-established with robust enterprise features | Complex configuration; XML overhead; limited mobile support |
| OAuth2 | API security, third-party integrations | Flexible and widely supported; ideal for microservices | Focuses only on authorization; prone to implementation errors |
| WebAuthn | Passwordless authentication, high-security environments | Eliminates passwords, reduces phishing, improves user experience | Limited support on some devices/browsers; still evolving |
Deployment Options: Self-Hosted vs Managed vs Hybrid
Self-hosted solutions offer complete control and customization, making them ideal for organizations with strong IT capabilities or strict compliance needs. However, they demand significant effort to manage maintenance, security updates, scaling, and disaster recovery.
Managed cloud services take care of infrastructure management, offering benefits like automatic updates, scalability, and high availability. Skycloak’s managed Keycloak hosting falls into this category, providing production-ready Keycloak instances with built-in monitoring, backups, and security hardening.
Hybrid deployments combine on-premises and cloud components, offering a middle ground. Sensitive data can remain on-premises for compliance, while user-facing services leverage the scalability of the cloud.
When choosing a deployment model, consider factors like your organization’s technical expertise, compliance requirements, and future growth plans. Review Skycloak’s pricing to compare the total cost of managed vs. self-hosted options.
Creating and Following Your Modernization Schedule
Important Steps in the Modernization Process
Requirements gathering: Begin by documenting user workflows, integration points, and success criteria. For mid-sized organizations, this phase typically takes 2-4 weeks.
Architecture design and vendor evaluation: Allocate 4-8 weeks to design your target architecture and evaluate vendors.
Pilot implementation: Roll out the new system to a small group — about 5-10% of users — for 6-12 weeks.
Phased rollout: Gradually expand the rollout, migrating 20-30% of users every 2-4 weeks.
Legacy system decommissioning: Once the new system proves stable, begin decommissioning legacy systems. This phase can take 3-6 months.
Setting Realistic Timelines
Small organizations may complete the process in 4-6 months, while mid-sized companies might need 8-12 months. Large enterprises often require 12-18 months or more.
Several factors influence the timeline:
- Resource availability: Organizations with dedicated identity management teams can progress faster.
- Application complexity: Modern web applications with standard protocols are easier to migrate, while legacy systems with custom authentication mechanisms can take months.
Managing Risks and Maintaining Operations
- Parallel system operation: Running old and new authentication systems simultaneously provides a fallback option.
- Gradual migration strategies: Begin with non-critical applications or volunteer user groups before moving to mission-critical systems.
- Rollback planning: Develop and test rollback procedures during pilot phases.
- Monitoring and alerting: Set up dashboards to track authentication success rates, response times, and error patterns.
- User communication: Keep users informed to reduce confusion and support tickets.
- Support team preparation: Equip help desk staff with training on new authentication flows.
Maintaining Security, Compliance, and Governance
Security Best Practices
- Adaptive MFA: Multi-factor authentication that adjusts based on risk factors helps reduce friction for low-risk activities while enhancing security during unusual or high-risk scenarios.
- Passwordless authentication with WebAuthn: This method reduces the risks associated with passwords and simplifies user support.
- Centralized RBAC: Centralized role-based access control simplifies permission management by allowing roles to be defined once and applied consistently.
- Zero-trust architecture principles: Modern protocols like OIDC and OAuth2 align naturally with zero-trust strategies.
- Session management policies: Modern protocols support advanced session controls. For more on this topic, see our guide on session management in distributed systems.
Compliance and Risk Management
- NIST Cybersecurity Framework: Emphasizes detailed documentation during authentication transitions.
- GDPR: Requires careful management of data flows and processing agreements.
- HIPAA: Modern protocols can simplify HIPAA compliance by improving audit trails and access controls.
- SOX compliance: Focus on access controls and segregation of duties.
Governance and Policy Updates
Key areas for policy updates include:
- Token lifecycle management: Define token validity periods and establish conditions for revocation.
- Federation trust criteria: Develop criteria for trusting external identity providers.
- Identity governance: Establish clear policies for managing identities across federated systems.
- Access governance: Move beyond traditional access reviews to understand how roles and permissions flow through federated systems.
- Incident response procedures: Prepare for authentication failures and security incidents involving multiple providers.
- Change management processes: Modern authentication systems require more sophisticated testing and rollback procedures.
Regular governance reviews are essential. Organizations should conduct quarterly reviews of authentication policies and annual assessments of the entire authentication architecture.
Conclusion: Building a Future-Ready Authentication System
Updating your authentication system is more than just a technical upgrade — it’s an investment in the security and flexibility of your digital operations. Transitioning from outdated methods to modern protocols lays the groundwork for handling new security challenges and meeting shifting business demands.
Modern authentication systems not only enhance security but also cut down on operational overhead, reduce support costs, and better support hybrid work environments.
However, modernization is not a one-time event — it’s an ongoing process. Integrating tools like passwordless authentication and adaptive multi-factor authentication is no longer optional for many; they are becoming baseline expectations.
For teams looking to modernize their authentication stack, Keycloak provides a robust open-source foundation supporting all major protocols. Skycloak’s managed hosting removes the infrastructure burden, allowing your team to focus on migration planning and application integration. Check the documentation for migration guides and best practices.
FAQs
What steps should organizations follow to upgrade from legacy authentication systems to modern protocols?
Start by evaluating your current identity environment to pinpoint dependencies, gaps, and potential challenges. Next, develop a detailed plan for the transition — you might opt for a phased or hybrid migration approach. Testing is critical — pilot migrations can help identify issues early. As you implement modern protocols like OIDC or SAML, consider integrating advanced features such as passwordless authentication or adaptive MFA.
What are the key differences between authentication protocols like OIDC, SAML, OAuth2, and WebAuthn?
OIDC is tailored for modern applications requiring both user authentication and identity information. SAML remains a staple for enterprise single sign-on, particularly in environments reliant on legacy systems. OAuth2 is designed to securely grant access to APIs without exposing user credentials. WebAuthn offers passwordless authentication by leveraging biometrics or hardware keys.
What compliance and security challenges might arise during authentication modernization?
Organizations often face hurdles like ensuring compliance with regulations such as GDPR, HIPAA, and CCPA, safeguarding sensitive information from breaches, and navigating the intricacies of hybrid or multi-cloud setups. To address these, craft a well-defined security strategy, regularly evaluate current systems, adopt robust multi-layered security practices, and ensure all authentication-related software and protocols are consistently updated.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.