Articles
Articles about articles from the Skycloak team.
Keycloak LDAP User Federation Explained
Understand LDAP federation in Keycloak with import users, edit modes, synchronization, LDAP mappers, and secure LDAPS setup.
SCIM Integration Between Okta and Keycloak
Learn SCIM provisioning from Okta to Keycloak with user sync, group sync, OAuth2 setup, and SCIM interoperability insights.

Okta vs Keycloak: Policies vs Authentication Flows Details
Compare Okta’s policy-based authentication with Keycloak’s flow-based model. Learn how MFA, fallback, and conditional access work in real-world IAM scenarios.

Keycloak 26.6+ Workflows: Automating Identity
Explore Keycloak 26.6 workflows to automate onboarding, enforce policies, and manage user lifecycle with simple YAML-based automation.
JWT Authorization Grant in Keycloak with Node.js
Learn how to implement JWT Authorization Grant in Keycloak 26.6 using a custom Node.js token issuer, including IDP setup, user…
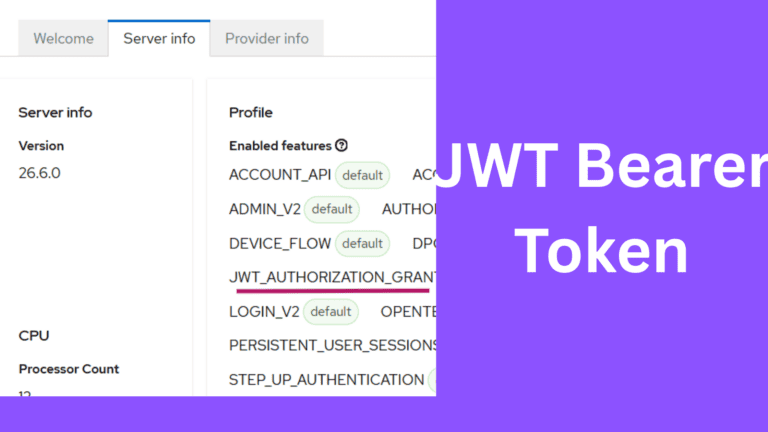
JWT Authorization Grant in Keycloak with External IdP
Learn how to implement JWT Authorization Grant in Keycloak using Auth0 as an external Identity Provider, including setup steps and…
Auth0 vs Keycloak: Login & Token Customization
Learn how Auth0 and Keycloak handle login control and token customization. Explore Actions, Authentication Flows, Protocol Mappers, and architecture trade-offs.
Keycloak CI/CD with GitHub Actions and Terraform
Learn how to automate Keycloak using Terraform and GitHub Actions. Build a CI/CD pipeline with secure secrets, plan, and apply…

Keycloak Configuration as Code with Terraform
Learn how to manage Keycloak using Terraform with Configuration as Code. Step-by-step guide with client setup, roles, and best practices.
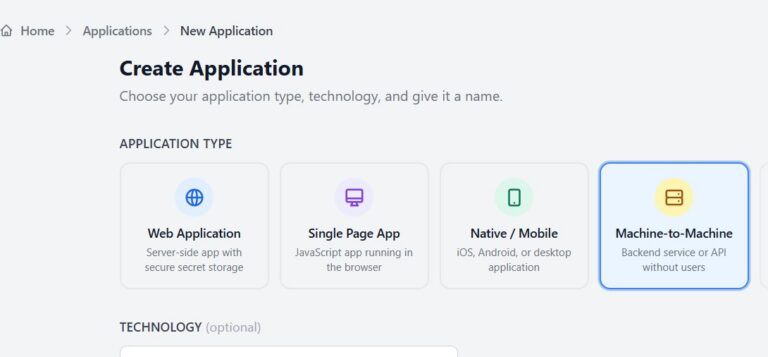
Client Credentials Flow with Skycloak and Node.js
Learn Client Credentials flow using Skycloak and Node.js. Implement secure machine-to-machine authentication with practical examples.
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.