Category
Articles
Articles about articles from the Skycloak team.
Articles
Why Choosing the Right Cybersecurity Certification Matters: Skycloak’s Journey with SFH Conseil
As a provider of secure identity and access management solutions, achieving the appropriate certification is critical for Skycloak. See how…
Articles
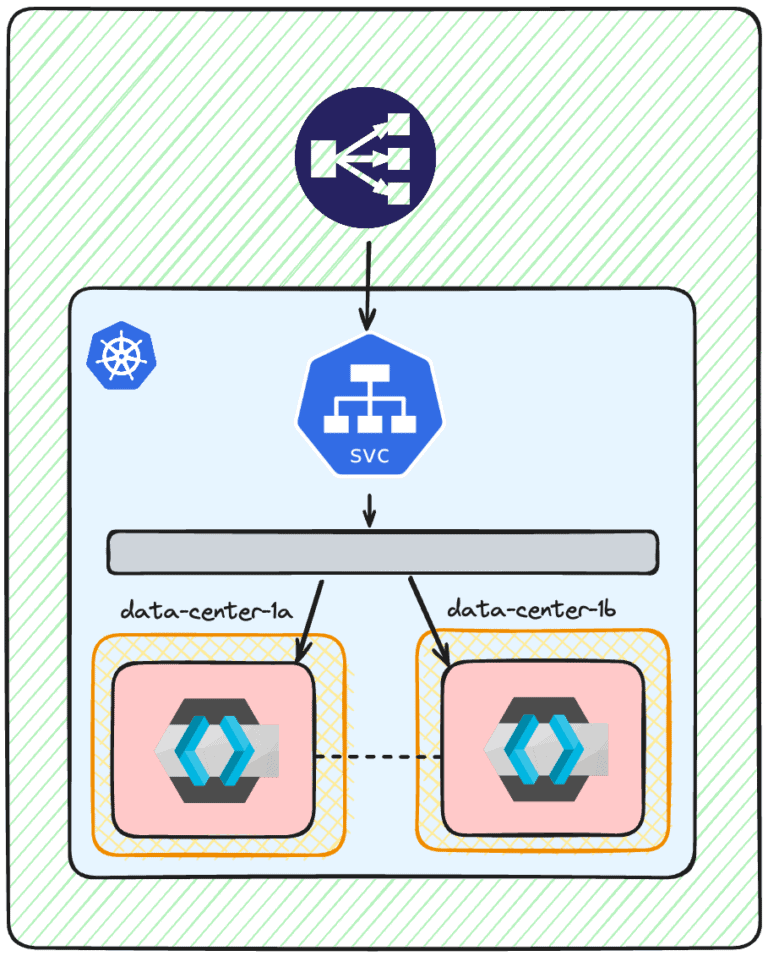
How to Achieve High Availability for Keycloak on Kubernetes
Discover how to deploy a highly available Keycloak cluster on Kubernetes. Learn how to optimize performance, reduce latency, and ensure…
Articles
Choosing the Best Authorization Flows for Your App
Understand and recognize the current OAuth and OIDC Authorization flows to secure your frontend applications effectively
Articles
The Top 11 Identity-as-a-Service (IDaaS) Powerhouses On The Market
In a world where “Top 10” lists are pretty common, we will take a path less traveled. Let’s explore the…

Articles
Zero Trust: A Thrilling New Era
I was recently discussing upcoming cybersecurity trends, and one topic kept popping up: Zero Trust. It’s a paradigm shift in…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.