OAuth 2.1: What Changed and How Keycloak Implements It
Last updated: March 2026
OAuth 2.0 has been the backbone of secure authorization for web and mobile applications for almost a decade. With the digital landscape evolving rapidly, a major update arrived: OAuth 2.1.
This version brings essential improvements, consolidating best practices and eliminating outdated features. If you’re a software engineer navigating the ever-changing tech world, this blog post will help you understand what changed in OAuth 2.1 and how it impacts your projects.
What is OAuth 2.1?
OAuth 2.1 is the latest version of the OAuth protocol, designed to streamline and secure the authorization process. While OAuth 2.0 served us well, it had some complexities and pitfalls that needed addressing. OAuth 2.1 simplifies implementation, enhances security, and incorporates the best practices established over the years.
Key Changes
Here are the major changes and improvements:
- Simplification of Flows
- Removal of Implicit Grant Flow: OAuth 2.1 deprecates the implicit grant flow due to its security vulnerabilities. Now, the authorization code flow with PKCE (Proof Key for Code Exchange) is the recommended approach for all client types, including SPAs (Single Page Applications).
- Authorization Code Flow with PKCE: PKCE, initially designed for public clients, is now mandatory for all clients. This adds an extra layer of security by requiring a secret code challenge.
- Enhanced Security
- Mandatory HTTPS: OAuth 2.1 mandates the use of HTTPS to ensure that all communication between the client and server is encrypted, preventing man-in-the-middle attacks.
- Refresh Tokens: Use of refresh tokens is recommended for obtaining new access tokens without user interaction. OAuth 2.1 promotes secure handling of refresh tokens, including binding them to the client using them.
- Deprecation of Unused Features
- Removal of Password Grant: The resource owner password credentials grant, commonly known as the password grant, is deprecated due to its poor security practices. Instead, OAuth 2.1 encourages using more secure flows like the authorization code flow.
- Simplified Client Registration: Version 2.1 introduces a simplified client registration process, reducing the overhead and complexity involved in setting up OAuth clients.
- Improved Developer Experience
- Clearer Specifications: OAuth 2.1 includes clearer and more concise specifications, making it easier for developers to understand and implement correctly.
- Best Practices and Recommendations: The new version consolidates best practices, offering guidance on secure implementation, handling tokens, and ensuring robust security.
How to Prepare?
As a software engineer, staying ahead of the curve is crucial. Here’s how you can prepare for OAuth 2.1:
- Review Your Current Implementations: Assess your current OAuth 2.0 implementations. Identify any usages of deprecated features like the implicit grant flow or password grant and plan for migration.
- Adopt Authorization Code Flow with PKCE: If you’re not already using PKCE, now is the time to start. Update your authorization flows to incorporate this security measure.
- Enforce HTTPS: Ensure that all your OAuth endpoints are served over HTTPS. This might involve configuring your servers and updating your client applications to use secure URLs.
- Securely Handle Tokens: Review how your application handles access and refresh tokens. Implement secure storage and transmission practices to prevent token leakage. Use the JWT Token Analyzer to inspect and debug your tokens during development.
- Stay Informed: Keep an eye on the official OAuth 2.1 specification and related announcements.
How Keycloak Implements OAuth 2.1
Keycloak has been at the forefront of implementing OAuth 2.1 requirements. Since version 24, Keycloak provides built-in OAuth 2.1 client profiles that enforce the new standards.
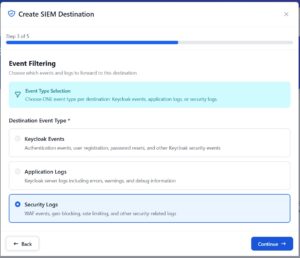
Enforcing OAuth 2.1 in Keycloak
To enforce OAuth 2.1 requirements on your Keycloak clients, you can use the built-in client policies and profiles:
-
Navigate to Realm Settings > Client Policies in the Admin Console.
-
Keycloak provides two pre-built OAuth 2.1 profiles:
- OAuth 2.1 Confidential Client Profile: Enforces PKCE, disallows implicit flow, requires client authentication, and mandates HTTPS redirect URIs.
- OAuth 2.1 Public Client Profile: Similar requirements but tailored for public clients (SPAs, mobile apps) that cannot store secrets securely.
-
Create a Client Policy that references one of these profiles and assign it to specific clients or apply it globally.
You can also manually configure individual clients to comply with OAuth 2.1:
- Disable the Implicit Flow: In Client Settings, ensure “Implicit Flow Enabled” is turned OFF.
- Require PKCE: Under Advanced Settings, set “Proof Key for Code Exchange Code Challenge Method” to
S256. - Disable Direct Access Grants: Turn off “Direct Access Grants Enabled” to block the password grant flow.
- Enforce HTTPS Redirect URIs: Only configure redirect URIs that use
https://(except for localhost during development).
For organizations looking to explore OAuth 2.1 alongside DPoP (Demonstration of Proof of Possession), see our guide on DPoP with Keycloak Admin API using Node.js. DPoP is a complementary security mechanism that binds tokens to specific clients, further strengthening token security beyond what OAuth 2.1 requires.
For more information about Keycloak’s OAuth 2.1 support, refer to the Keycloak documentation on client policies.
Conclusion
OAuth 2.1 is a significant step forward in securing the authorization process for web and mobile applications. By simplifying flows, enhancing security, and deprecating outdated features, OAuth 2.1 makes it easier for developers to implement robust and secure authorization mechanisms.
As a software engineer, embracing these changes ensures that your applications remain secure and compliant with the latest standards. Review your current implementations, adopt the new best practices, and stay informed about changes. With OAuth 2.1 and Keycloak’s built-in support, you’ll be well-equipped to navigate the future of secure authorization.
To get started with a Keycloak instance that supports OAuth 2.1 out of the box, check out Skycloak’s managed hosting — deploy production-ready Keycloak in minutes with single sign-on and all modern authentication protocols pre-configured. Read the documentation for setup guides and best practices.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.