Keycloak WebAuthn Passwordless with Passkeys
Last updated: March 2026
Introduction
In this article, we look at how to use Passkeys with Keycloak for passwordless authentication.
For demonstration, I am using Keycloak 26.4.5.
What is a Passkey? (as per the FIDO Alliance)
A passkey is a FIDO authentication credential based on FIDO standards that allows users to sign in to apps and websites using the same mechanism they use to unlock their device — biometrics, PIN, or pattern.
Passkeys are cryptographic credentials tied to a user’s account on a website or application. They eliminate the need for passwords.
If you’re curious about the broader passwordless movement, read our post on why everyone is talking about passwordless authentication.
Platform Authenticators vs. Roaming Authenticators
Passkeys can be created using two types of authenticators:
- Platform authenticators are built into the device (e.g., Touch ID on Mac, Windows Hello, Android biometrics). These passkeys are tied to the specific device and cannot be moved, though some platforms now support cloud syncing (iCloud Keychain, Google Password Manager).
- Roaming authenticators are external hardware security keys (e.g., YubiKey, Titan Security Key) that can be used across multiple devices via USB, NFC, or Bluetooth.
When configuring Keycloak’s WebAuthn policy, the Authenticator Attachment setting controls which types are allowed: platform (device-only), cross-platform (roaming-only), or unset (both allowed). For most deployments, leaving this unset gives users maximum flexibility.
Additional Overview
Before using WebAuthn, a user must register a WebAuthn credential with Keycloak.
Keycloak acts as the Relying Party (RP), and the other components are:
- Browser
- Authenticator (built-in device authenticator or external hardware)
- User
WebAuthn works using public-private key cryptography. During registration:
- A public-private key pair is generated.
- The private key stays securely on the user’s authenticator (device or security key) and never leaves it.
- The public key is sent to Keycloak and stored in its database for future authentication.
For a detailed explanation of the WebAuthn specification, see the W3C WebAuthn documentation.
Login Flow After Registration
Once registration is complete, a login attempt works like this:
- User tries to authenticate at Keycloak.
- Keycloak sends a challenge to the browser.
- The browser invokes
navigator.credentials.get(), which interacts with the authenticator. - The authenticator signs the challenge with the private key.
- The signed challenge is returned via the browser to Keycloak.
- Keycloak verifies the signature using the stored public key.
- If the signature is valid, the user session is created.
In Keycloak, WebAuthn can be used as:
- First-factor authentication (passwordless login)
- Second-factor authentication (after username/password) — covered in our follow-up article on enabling passkeys for 2FA
Configuring Passkey
Starting with Keycloak version 26.4, passkeys can be configured more easily as per the Keycloak passkey documentation.
In this article, we look at how to use passkeys for first-factor authentication.
First, ensure that you are using a supported version of Keycloak.
Enabling Passkeys
Preliminary Settings
Go to:
Realm Settings -> Authentication -> Policies -> WebAuthn Passwordless Policy
- Turn Enabled Passkeys = ON
It is also recommended to keep the following settings at their default values:
- Require discoverable credentials = Yes
- User Verification requirement = Required
For full documentation on WebAuthn policies, see the Keycloak WebAuthn documentation.
Registering the User
A user can register a passkey using the built-in Account Console after logging in through the normal username/password flow:
Account Settings -> Signing In
If you have reviewed the documentation linked earlier, you will notice that the default browser authentication flow already supports first-factor passkey login. (We have to set Passkeys to ON as described in the beginning of this article.)
Testing the Implementation
Access your client application or the built-in Account Console.
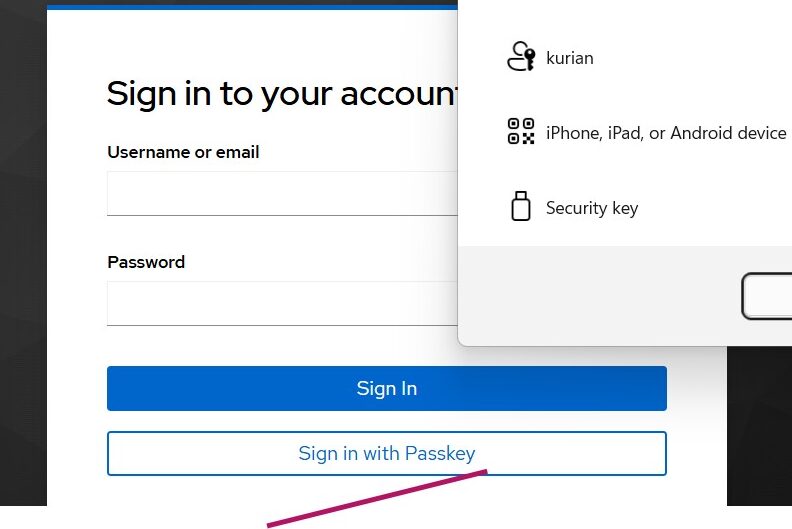
Click Sign in with Passkey and select the passkey you created during registration in the Account Console.
Summary
In this article, we explored how to use Passkeys in Keycloak as a first-factor authentication method. With passkeys, users get a secure, phishing-resistant, password-free login experience powered by the FIDO2 standards.
Passkeys represent a significant step forward for multi-factor authentication and user experience. Combined with Keycloak’s flexible authentication flows, they provide a strong security foundation for modern applications.
Skycloak provides production-ready managed Keycloak hosting, helping teams avoid the complexity of maintaining and scaling Keycloak themselves.
If you’re new to Skycloak, visit the Skycloak Getting Started Guide to learn more.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.
