Identity Service Procurement: Contract Negotiation and SLA Requirements

Last updated: March 2026

Identity and Access Management (IAM) is critical for securing digital operations, especially in cloud-first and remote work environments. Poorly structured contracts or weak Service Level Agreements (SLAs) can lead to security breaches, compliance failures, and operational downtime. This guide outlines key considerations for procuring IAM services, including contract essentials, SLA metrics, compliance needs, and vendor evaluation.
Key Takeaways:
- Contracts: Define service scope, liability limits, data ownership, and termination procedures to protect your organization.
- SLAs: Focus on uptime guarantees, response times, and incident management to minimize disruptions. See how Skycloak’s SLA compares to industry benchmarks.
- Compliance: Ensure vendors meet standards like SOC 2, GDPR, or HIPAA, and include audit rights and breach notification timelines.
- Vendor Selection: Assess security practices, certifications, and financial stability to choose a reliable provider.
- Data Management: Specify encryption, backup, and data portability requirements to ensure long-term control and security.
IAM procurement requires precise planning, detailed agreements, and ongoing vendor management to safeguard your organization’s digital infrastructure.
Contract Negotiation Requirements
Securing an IAM solution requires contracts that safeguard your organization’s interests while ensuring uninterrupted operations. A well-structured contract is not just a formality — it’s a critical tool to manage risks and set expectations.
Core Contract Elements
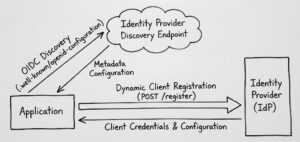
The scope of services is the backbone of any IAM contract. Clearly outline all services included, such as SSO, MFA, user provisioning, integration capabilities, supported protocols (e.g., SAML 2.0, OpenID Connect), and limits on users or applications. Ambiguity here can lead to misunderstandings down the line.
When it comes to service availability commitments, precision is key. Define uptime standards, allowable maintenance windows, and criteria for partial outages, as these can disrupt operations just as much as full outages. Specify how these disruptions will be addressed and what remedies are available.
Liability and indemnification clauses should reflect the real-world impact of IAM failures. While vendors often limit liability to the contract value, the fallout from an IAM failure — such as a security breach — can far exceed subscription fees. Negotiate liability caps that match potential risks, and insist on indemnification clauses that cover damages from security breaches caused by vendor negligence.
With stricter privacy regulations, data residency requirements have become essential. Specify where identity data will be stored, restrict cross-border processing if needed, and establish clear notification protocols for any changes.
Performance guarantees should go beyond basic uptime. Include measurable benchmarks for operations like authentication response times, provisioning, and recovery, ensuring minimal disruption to business processes.
Compliance Requirements
IAM services often intersect with various regulatory frameworks, making compliance a vital part of the contract. Address audit rights, reporting obligations, and the management of regulatory changes, ensuring alignment with standards like SOC 2, ISO 27001, GDPR, HIPAA, and PCI DSS.
Audit rights should allow your organization to verify the vendor’s security controls. This could include conducting direct audits or reviewing third-party audit reports. Specify the frequency of these reviews, the scope of areas to be examined, and the vendor’s response time for providing documentation.
Breach notification requirements must align with your regulatory needs. For instance, GDPR mandates breach notifications within 72 hours, while HIPAA allows up to 60 days. Your contract should require the vendor to notify you promptly and provide detailed information to meet reporting requirements.
Data Protection and Termination Clauses
Effective data management and clear termination procedures are vital to maintaining operational stability and protecting sensitive information.
Specify encryption standards for data at rest (e.g., AES-256) and data in transit (e.g., TLS 1.3), along with key management protocols.
When transitioning vendors or bringing services in-house, data portability requirements are crucial. The contract should specify export formats like SCIM or LDIF, and include provisions for receiving data in multiple formats.
Termination procedures must address the return or destruction of data. Include timelines and milestones for different data types, and require written certification of data destruction.
SLA Requirements and Evaluation
Service Level Agreements (SLAs) transform vendor promises into measurable commitments, defining performance standards, response times, and remedies when expectations are not met.
Core SLA Metrics
One of the most critical SLA components is uptime guarantees. For instance, a 99% uptime means nearly three days of annual downtime, while 99.9% limits downtime to roughly 8 hours and 45 minutes per year.
Response time commitments should clearly define acknowledgment and resolution timeframes. For critical incidents, SLAs should demand acknowledgment and resolution within an hour, while less urgent issues may allow for longer windows.
SLA Benchmarks and Comparisons
| SLA Tier | Uptime Guarantee | Annual Downtime | Critical Response | Use Case |
|---|---|---|---|---|
| Basic | 99.5% | ~44 hours | 4-8 hours | Small businesses, non-critical systems |
| Standard | 99.9% | ~8.75 hours | 1-2 hours | Mid-market, standard business operations |
| Premium | 99.95% | ~4.4 hours | 15-60 minutes | Enterprise, business-critical applications |
| Mission-Critical | 99.99% | ~53 minutes | 15-30 minutes | Large enterprises, zero-tolerance systems |
To understand how Skycloak’s SLA commitments compare, see the Skycloak SLA page.
SLA Monitoring and Enforcement
Clarity in SLA metrics is critical — vague language can lead to disputes and weaken the agreement’s value. Establishing Key Performance Indicators (KPIs) aligned with SLA terms is a practical way to track vendor performance.
Regular SLA reviews are a must. Schedule quarterly or semi-annual reviews to evaluate whether the current terms still meet your operational requirements.
Enforcement mechanisms should include financial penalties that account for the true cost of service failures.
Architecture and Protocol Decisions for Identity Services
Self-Hosted vs. Managed IAM Solutions
Deciding between self-hosted and managed IAM solutions is a critical step.
| Factor | Self-Hosted | Managed Service |
|---|---|---|
| Initial Investment | High capital expenditure | Lower upfront costs |
| Operational Control | Full system control | Limited configuration options |
| Compliance | Direct audit trail | Vendor-dependent compliance |
| Scalability | Manual planning required | Automatic scaling |
| Security Updates | Handled internally | Vendor-managed patching |
| Expertise Requirements | High internal expertise needed | Vendor provides expertise |
| Contract Complexity | Focus on software licensing | Emphasis on SLA commitments |
Managed services like Skycloak’s hosted Keycloak handle infrastructure, updates, and security patching, letting your team focus on application development. Evaluate the pricing to understand total cost of ownership compared to self-hosting.
For organizations looking to quantify the financial impact of their IAM decisions, the IAM ROI Calculator can help model costs across different deployment models.
IAM Procurement Best Practices
Vendor Due Diligence
Evaluating security practices begins with a detailed review of the vendor’s internal protocols. Request documentation on their security architecture, incident response plans, and employee access controls.
Compliance certifications help establish trust. SOC 2 Type II reports provide insights into the effectiveness of a vendor’s controls over time. ISO 27001 certification highlights a commitment to managing information security systems effectively.
Common Procurement Mistakes and How to Avoid Them
- Overlooking exit planning can result in expensive complications.
- Unclear data ownership and residency can lead to compliance headaches.
- Vague SLAs often lead to disputes.
- Ignoring integration requirements can result in expensive customizations.
- Insufficient compliance coverage can expose your organization to regulatory risks.
- Skipping financial due diligence can leave you vulnerable to service disruptions.
Conclusion
Securing the right IAM solution requires a careful balance of technical requirements, financial considerations, and future scalability. The contracts you sign and the service level agreements (SLAs) you establish will directly influence your security posture and operational efficiency.
Modern IAM procurement is undeniably complex, but organizations that focus on detailed contract negotiations, tailored SLAs, and strategic alignment across architecture and vendor management set themselves up for lasting success. Your identity infrastructure is a critical asset, and the effort you invest in these practices will safeguard your organization’s most valuable digital resources.
FAQs
What are the main differences between self-hosted and managed IAM solutions, and how should they influence your procurement decisions?
Self-hosted IAM solutions provide organizations with complete control over their infrastructure, allowing extensive customization. However, they demand substantial technical expertise and dedicated resources. Managed IAM solutions transfer much of the operational burden to the vendor, offering benefits like automatic updates, scalability, and quicker deployment.
Choosing between these options depends on your organization’s technical capabilities, budget, and long-term scalability requirements.
What should organizations include in IAM service contracts and SLAs to ensure compliance with regulations like GDPR and HIPAA?
Key provisions to include are: Data processing agreements (DPAs), breach notification protocols, and compliance with standards such as SOC 2, ISO 27001, or other relevant certifications. It’s equally important to include terms for regular audits, enforce data encryption requirements, and ensure the vendor is held accountable for meeting applicable legal and regulatory standards.
What are common mistakes to avoid when procuring IAM services?
Common missteps include paying for features you don’t need, accepting generic SLAs that fail to meet your unique requirements, and having minimal options for addressing SLA violations. Begin by thoroughly assessing your organization’s specific needs, pinpoint critical elements like uptime guarantees, response times, and compliance requirements, and push for vendor accountability.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.