Skycloak’s SOC 2 Journey: From Type 1 to Type 2 Certification
Last updated: March 2026
When your identity provider handles every login, token issuance, and session in your application stack, the security posture of that infrastructure is not a nice-to-have — it is foundational. Your customers trust you with their credentials, and you trust your identity platform to protect them. That chain of trust demands verification.
That is why we pursued SOC 2 certification for Skycloak. We completed our SOC 2 Type 1 audit in December 2024 and our SOC 2 Type 2 audit in April 2025. This post explains what SOC 2 is, what distinguishes Type 1 from Type 2, what we had audited, and what this means for teams that rely on Skycloak as their managed Keycloak hosting platform.
What Is SOC 2?
SOC 2 (System and Organization Controls 2) is an auditing framework developed by the American Institute of Certified Public Accountants (AICPA). It evaluates how a service organization manages data based on five Trust Services Criteria:
- Security — Protection of information and systems against unauthorized access. This is the baseline criterion that every SOC 2 audit includes.
- Availability — The system is operational and accessible as committed or agreed upon.
- Processing Integrity — System processing is complete, valid, accurate, and timely.
- Confidentiality — Information designated as confidential is protected as committed.
- Privacy — Personal information is collected, used, retained, disclosed, and disposed of in accordance with the organization’s privacy notice.
Unlike certifications that check a box at a single moment, SOC 2 is designed to assess whether an organization has built and maintains effective controls over time. For identity infrastructure — where a single misconfiguration can expose authentication flows to compromise — this kind of ongoing scrutiny is exactly what customers should demand from their providers.
Type 1 vs. Type 2: What Is the Difference?
SOC 2 comes in two report types, and the distinction matters.
SOC 2 Type 1 evaluates the design of controls at a specific point in time. The auditor reviews whether the controls a company has put in place are suitably designed to meet the relevant Trust Services Criteria. Think of it as a snapshot: on this date, were the right controls in place?
SOC 2 Type 2 goes further. It evaluates both the design and the operating effectiveness of those controls over an observation period, typically three to twelve months. The auditor does not just confirm that controls exist — they verify that those controls were consistently applied and effective throughout the entire review window.
Type 2 is the standard that enterprise security teams look for during vendor evaluations because it demonstrates sustained operational discipline, not just a one-time setup.
Our SOC 2 Type 1 Journey (December 2024)
We completed our SOC 2 Type 1 audit in December 2024. This was the starting point of our compliance program and required us to formalize and document controls across every layer of the Skycloak platform.
The Type 1 process involved a thorough assessment of our security posture at that point in time. The auditor examined our policies, procedures, and technical controls to determine whether they were properly designed to protect customer data and maintain system reliability.
Preparing for the Type 1 audit pushed us to codify practices that we had been following informally and to close gaps where documentation or process rigor did not yet meet the bar. Areas of focus included:
- Infrastructure security architecture and network segmentation
- Access control policies and least-privilege enforcement
- Monitoring and alerting across our hosting environment
- Incident response procedures and escalation paths
- Encryption standards for data at rest and in transit
- Change management processes for platform updates
Achieving Type 1 confirmed that our controls were well-designed. But design alone is not enough — controls need to work reliably over time. That is what Type 2 addresses.
Advancing to SOC 2 Type 2 (April 2025)
Following the Type 1 milestone, we moved directly into the observation period for our SOC 2 Type 2 audit. During this window, an independent auditor monitored whether the controls we had in place were operating effectively on an ongoing basis.
We completed the SOC 2 Type 2 audit in April 2025. This report confirms that our security controls were not only properly designed but consistently enforced throughout the observation period.
The Type 2 audit examined evidence across months of operations. This included reviewing access logs, change records, incident reports, monitoring data, and internal review processes. The auditor verified that what we documented in our policies matched what actually happened in practice — day after day, across every part of the platform.
For our customers, the Type 2 report is the stronger signal. It demonstrates that Skycloak maintains its security commitments continuously, not just when someone is watching.
What We Had Audited
Our SOC 2 audits covered the controls that are most critical to a managed identity infrastructure platform. Here is a summary of the key areas:
Infrastructure Security
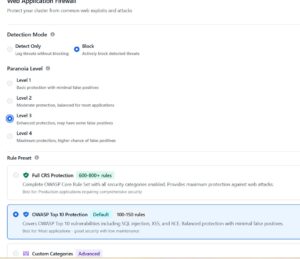
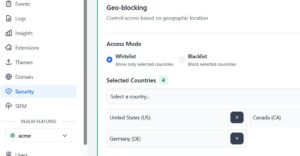
Skycloak runs on hardened infrastructure with network-level isolation between customer environments. Our audit covered the architecture of our hosting environment, firewall rules, and the measures we use to prevent unauthorized access at every layer. For more detail on our security practices, visit our security page.
Access Controls
We enforce strict access control policies internally. The audit reviewed how we manage team access to production systems, including role-based permissions, multi-factor authentication requirements, and regular access reviews. These same principles underpin the user management and RBAC capabilities we provide to customers.
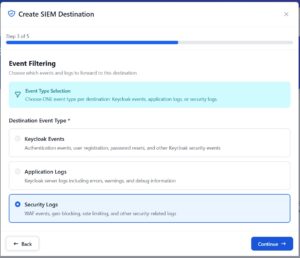
Monitoring and Logging
Continuous monitoring is central to both our compliance program and our platform. The audit examined our logging infrastructure, alerting rules, and how we detect and respond to anomalous activity. Our audit logs feature gives customers the same level of visibility into their own Keycloak environments.
Incident Response
The audit assessed our incident response plan, including detection, triage, communication, and remediation procedures. We maintain documented runbooks and conduct regular reviews to ensure the team can respond quickly when issues arise.
Data Encryption
All customer data is encrypted at rest and in transit. The audit verified our encryption standards, key management practices, and the controls we have in place to protect sensitive information throughout its lifecycle.
Change Management
Platform updates, configuration changes, and infrastructure modifications all follow a documented change management process. The audit reviewed how we test, approve, and deploy changes to ensure that updates do not introduce security regressions.
What This Means for Skycloak Customers
SOC 2 Type 2 certification has practical implications for teams evaluating or already using Skycloak.
Reduced Vendor Risk Assessments
Many organizations require SOC 2 Type 2 reports from their vendors before onboarding. Having this report available streamlines your procurement and security review process. Instead of lengthy questionnaire exchanges, your security team can review our SOC 2 report directly.
Enterprise Readiness
For teams building products that serve regulated industries — healthcare, financial services, government — your own compliance posture depends on the compliance posture of your vendors. Skycloak’s SOC 2 Type 2 certification supports your compliance obligations whether you are pursuing SOC 2, HIPAA, or ISO 27001 for your own organization.
Confidence in Operational Security
The Type 2 report confirms that our security controls work in practice, not just on paper. This means the infrastructure hosting your Keycloak instances, the systems managing your identity providers, and the platform handling your security events are all protected by controls that have been independently verified.
Transparency
We believe that trust is built through transparency. If you are a customer or prospective customer and would like to review our SOC 2 Type 2 report, contact us and we will share it under NDA.
Our Ongoing Commitment
SOC 2 is not a one-time achievement. Maintaining certification requires continuous adherence to the controls and processes that were audited. We are committed to:
- Annual SOC 2 Type 2 renewals to ensure our controls remain effective as the platform evolves
- Continuous monitoring of our infrastructure, access patterns, and security events
- Regular internal reviews of policies and procedures to keep pace with emerging threats and industry best practices
- Investing in security tooling to strengthen detection, prevention, and response capabilities
Security is a core part of the Skycloak platform, not an afterthought. You can read more about our approach on the security page or explore the security features available in your Keycloak environment through our documentation.
Conclusion
Achieving SOC 2 Type 2 certification is a milestone we are proud of, but it is also just one part of an ongoing commitment to securing identity infrastructure for our customers. From our Type 1 audit in December 2024 through our Type 2 completion in April 2025, we have built a compliance program that reflects how seriously we take the responsibility of managing authentication and identity for production applications.
If you are evaluating managed Keycloak providers and compliance is a factor in your decision, we would be happy to share our SOC 2 Type 2 report and discuss how Skycloak meets your security requirements.
Ready to get started? Explore our plans or reach out to our team to learn more.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.