Auth0 vs Keycloak: Login & Token Customization
Introduction
When working with Identity Platforms, a common requirement is:
Control who can log in and customize what goes into tokens.
Both Auth0 and Keycloak support this—but their approaches are fundamentally different. This article compares how each platform handles post-login customization and token enrichment, and what it means for architects and developers.
Design Philosophy
Auth0
- Developer-first approach
- Customization via JavaScript-based Actions
- Inline logic execution during authentication
Keycloak
- Configuration-first approach
- Customization via:
- Authentication Flows
- Protocol Mappers
- Authorization Policies
- Deep extensibility via Java-based SPI
🔄 Authentication Flow Comparison
Below diagram illustrates how post-login customization differs between Auth0 and Keycloak:
📊 Auth0 Action vs Keycloak Flow
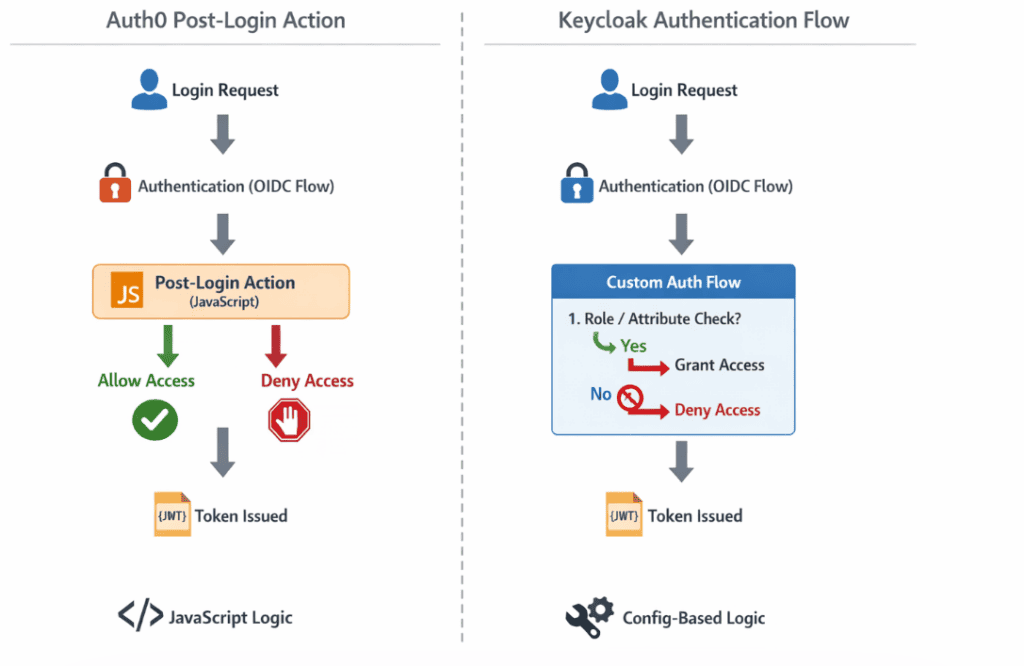
Key Insight
- Auth0 executes custom logic using JavaScript during login
- Keycloak evaluates conditions via configured authentication flows
Post-Login Logic (Access Control)
Auth0 Approach: Actions (Post-Login)
Auth0 allows developers to write JavaScript logic that runs immediately after authentication.
Example:
if (event.user.app_metadata.role !== "premium") {
api.access.deny("Access restricted");
}
✔️ Simple
✔️ Centralized
✔️ Highly flexible
Keycloak Approach: Authentication Flows
Keycloak does not provide a direct scripting hook like Auth0. Instead, it uses Authentication Flows.
You can:
- Add conditions:
- User Role
- User Attribute
- Configure execution:
- Allow access
- Deny access
✔️ No code required
✔️ UI-driven configuration
✔️ Predictable execution model
⚠️ JavaScript Customization in Keycloak
Earlier versions of Keycloak supported:
- Script Authenticators
- JavaScript-based policies
However:
In modern Keycloak versions (Quarkus-based, v17+ and beyond), JavaScript execution is disabled by default and discouraged for production use.
Why?
- Security concerns
- Performance overhead
- Maintainability challenges
👉 This is a key architectural difference compared to Auth0.
Token Customization
Auth0: Dynamic Token Enrichment
Auth0 uses Actions to modify tokens dynamically.
Example:
api.idToken.setCustomClaim("https://example.com/role", "admin");
✔️ Flexible
✔️ Dynamic
✔️ Code-driven
Keycloak: Protocol Mappers
Keycloak uses Protocol Mappers to customize tokens.
You can:
- Add user attributes
- Add roles (realm/client)
- Add static or computed claims
✔️ Declarative
✔️ No scripting required
✔️ Built-in and standardized
For more details on OpenID Connect token structure, refer to the official specification available here.
Extensibility Model
Auth0
- JavaScript-based extensibility
- Limited to predefined hooks
Keycloak
- Enterprise extensibility via SPI:
- Authenticator SPI
- User Storage SPI
- Event Listener SPI
✔️ Extremely powerful
❌ Requires Java development
⚖️ Trade-offs
| Feature | Auth0 | Keycloak |
|---|---|---|
| Post-login customization | ✅ JS Actions | ⚠️ Authentication Flows |
| Token customization | ✅ JS | ✅ Protocol Mappers |
| Runtime scripting | ✅ Yes | ❌ Disabled by default |
| Ease of use | ✅ High | ✅ High |
| Flexibility | ⚠️ Hook-based | ✅ Very high (SPI) |
| Extensibility | ⚠️ Limited | ✅ Enterprise-grade |
Architectural Insight
Auth0 optimizes for:
Developer agility with inline scripting
Keycloak emphasizes:
Predictable, declarative configuration with extensibility through compiled components (SPI)
When to Use What
Choose Auth0 if:
- You prefer JavaScript-based hooks
- You are not concerned if costs escalates at scale
Choose Keycloak (Skycloak- managed Keycloak) if:
- You need full IAM control
- You prefer open-source solutions
- You need deep extensibility
- Comparatively lower price at scale
Summary
While Auth0 provides a more developer-friendly scripting model, Keycloak offers a robust and scalable configuration-driven approach.
In modern Keycloak deployments, most customization can be achieved using authentication flows and protocol mappers, without writing custom code.
About Skycloak
Skycloak is a fully managed Keycloak platform hosted in the cloud. It enables organizations to leverage the power of open-source Keycloak IAM without the operational overhead of installing, maintaining, and scaling production-grade Keycloak environments — delivered securely and cost-effectively.
If you’re new to Skycloak, visit the Skycloak Getting Started Guide to learn more
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.