Definition and Basics
Articles about definition and basics from the Skycloak team.
IoT Identity Management: Securing Connected Devices with Keycloak
Learn how to implement IoT identity management with Keycloak. This guide covers OAuth 2.0 Device Authorization Grant, machine-to-machine authentication, Zero…
How Digit Code Crackers Operate: What You Need to Know
Unveil the inner workings of digit code crackers and find out what steps you can take to safeguard your digital…
Getting Started with Python Authentication for IAM
Unlock the power of Python authentication for IAM! Dive into step-by-step guides, real-world scenarios, and best practices to enhance your…
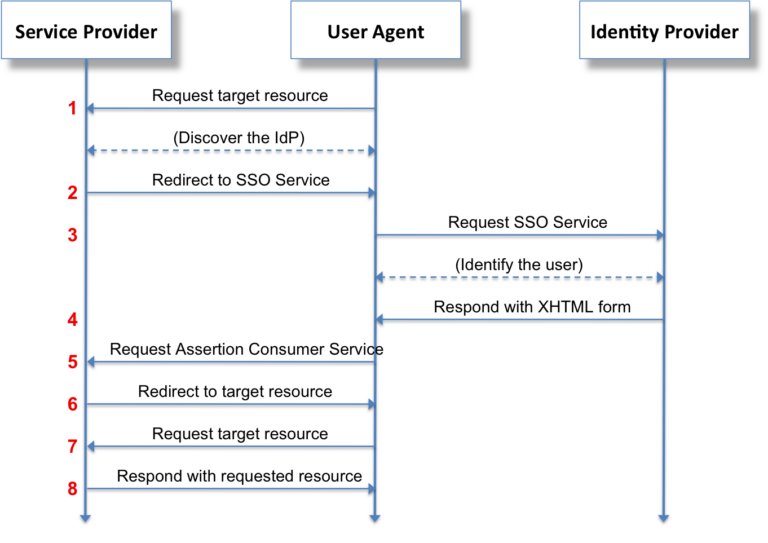
Decoding SamlRequest: SAML Simplified for Everyone
Ever felt puzzled by SamlRequest in your SAML authentication flow? 🤔 Unlock its secrets and discover how to enhance your…
Keycloak Integrations: An Overview for Enterprises
Discover the power of Keycloak integrations in enterprise environments. Learn how to enhance security, streamline authentication, and overcome common challenges…
Is OAuth the Same as SSO? A Beginner’s Guide
Confused about OAuth and SSO? 🤔 You're not alone! Dive into our beginner's guide to demystify these authentication concepts and…
Understanding the Difference Between SSO and SAML
Confused about SSO and SAML? 🤔 You're not alone! Dive into this detailed guide to demystify these authentication concepts and…
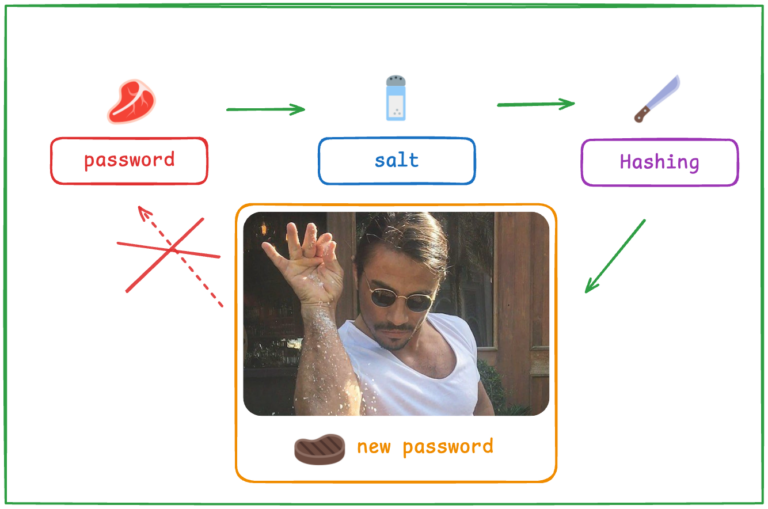
Bcrypt: Why It’s a Preferred Password Hashing Algorithm
Unveil the secrets of bcrypt and learn why it's still a preferred password hashing algorithm. Dive into its basics, real-world…

Device Management in IAM: An Introduction
Unlock the potential of device management in IAM with Keycloak. Learn how to secure devices, address challenges, and implement best…
Exploring Auth0 Alternatives: What’s Right for You?
Looking to move beyond Auth0? Dive into our comprehensive guide on top alternatives, including Keycloak, to find the right fit…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.