Session Management in Distributed Systems: Cookies vs Tokens vs Server-Side Sessions

Last updated: March 2026

Session management is essential for maintaining user state across HTTP requests, especially in distributed systems where challenges like scalability, consistency, and security become more complex. This guide compares three common methods — cookies, tokens, and server-side sessions — to help you choose the best approach for your architecture.
Key Takeaways:
- Cookies: Simple to implement and browser-supported but prone to CSRF and scaling issues.
- Tokens (e.g., JWT): Stateless and scalable, ideal for microservices, but revocation is challenging.
- Server-Side Sessions: Secure and centralized, offering immediate revocation, but harder to scale in distributed setups.
Quick Comparison:
| Aspect | Cookies | Tokens (JWT) | Server-Side Sessions |
|---|---|---|---|
| Security | Requires flags for protection | Vulnerable if leaked | Stronger due to central control |
| Scalability | Limited, needs sticky sessions | Scales well, stateless | Constrained by storage limits |
| Performance | Minimal network overhead | Lightweight validation | Slower due to lookups |
| Revocation | Immediate via server deletion | Harder, requires blacklists | Instant and reliable |
| Cross-Domain Support | Limited, domain-specific | Excellent, works across domains | Needs extra setup |
Choosing the Right Method:
- Use Cookies for simple web apps with limited scaling needs.
- Opt for Tokens in microservices or globally distributed systems.
- Prefer Server-Side Sessions for secure, compliance-heavy environments.
Each method has trade-offs, so align your choice with your system’s security, scalability, and compliance needs. Hybrid approaches can also combine the strengths of multiple methods.
Session Management with Cookies
How Cookies Work in Session Management
Cookies are small text files that browsers store and send with each HTTP request to the same domain. When a user logs into an application, the server generates a unique session identifier and sends it back to the browser as a cookie. This cookie is then included in all subsequent requests, enabling the server to recognize the user and maintain their session state.
In distributed systems, cookies typically serve one of two roles: they either carry a session identifier (session cookies) or embed data directly (persistent cookies). Session cookies are generally preferred for sensitive information, as they keep the data on the server rather than exposing it in the browser.
To enhance security, browsers enforce attributes like HttpOnly, Secure, and SameSite:
HttpOnly: Prevents JavaScript from accessing the cookie, reducing the risk of Cross-Site Scripting (XSS) attacks.Secure: Ensures cookies are only transmitted over HTTPS, protecting them from interception on unsecured networks.-
SameSite: Controls whether cookies are sent with cross-site requests. Options include:- Strict: Cookies are not sent with any cross-site requests.
- Lax: Cookies are sent with top-level navigation but not with embedded content.
- None: Cookies are sent with all requests but require the
Secureattribute.
In distributed architectures, managing cookie scope and domain is essential. Cookies can be scoped to specific domains or paths, which determines their accessibility.
Cookie Security Risks and Protection
Cookies, while convenient, come with several security risks. One major concern is Cross-Site Request Forgery (CSRF), which exploits the browser’s automatic cookie inclusion to perform unauthorized actions on behalf of the user. To counter this, servers often use CSRF tokens — unique and unpredictable values included in forms or AJAX requests.
Another significant threat is Cross-Site Scripting (XSS). Malicious scripts running in a user’s browser can potentially access and steal session cookies. The HttpOnly, Secure, and SameSite attributes discussed earlier are vital defenses against such attacks.
Cookie hijacking is another risk, where attackers intercept cookies over unsecured networks. This highlights the importance of implementing SSL/TLS across all services to safeguard session data in transit.
Additionally, regenerating session IDs after authentication can protect against session fixation attacks, where attackers attempt to exploit an existing session ID.
Cookie Performance and Scaling Issues
The size of cookies directly impacts network performance, as each cookie adds to HTTP headers. Browsers typically limit cookies to 4KB each and a total of 4MB per domain. In distributed systems with multiple services, large cookie sizes can create noticeable performance bottlenecks.
Some systems use sticky sessions for load balancing, which ties a user’s session to a specific server. While this simplifies cookie management, it limits scalability and introduces risks. If the server handling sticky sessions goes down, users lose their sessions and must re-authenticate.
Cross-domain limitations add another layer of complexity. Cookies are naturally confined to their assigned domains, which can complicate session management for organizations operating across multiple domains or integrating third-party services.
Token-Based Session Management
How Tokens Work for Sessions
Tokens provide an alternative approach to managing sessions. Instead of relying on server-side storage to hold session data, tokens encapsulate session information directly within the token itself, making them self-contained.
A widely used example is the JSON Web Token (JWT), which has three components separated by dots: the header, payload, and signature. The header specifies the signing algorithm, the payload contains session-related data (known as claims), and the signature ensures the token’s integrity. You can use the JWT Token Analyzer to inspect and decode JWTs during development.
For those seeking stronger security defaults, PASETO (Platform-Agnostic Security Tokens) offers an alternative. Unlike JWT, which allows developers to choose algorithms that may not be secure, PASETO enforces built-in cryptographic protocols designed to minimize risks.
One of the standout features of tokens is their statelessness. When a client sends a token with a request, the server validates its signature and extracts the session data directly from the token. This eliminates the need for server-side session storage.
Tokens often utilize Bearer authentication, where the client includes the token in the HTTP Authorization header like this: Authorization: Bearer <token>. This method works well across various domains and services, making it a go-to choice for distributed systems.
Another key feature of tokens is their built-in expiration mechanism. Unlike traditional sessions that depend on server-side timeouts, tokens carry their own expiration timestamp. For a deeper exploration of token lifecycle strategies, see our guide on JWT token lifecycle management.
Token Security Risks and Mitigation
While token-based authentication offers flexibility, it also introduces specific security challenges. Token leakage is one of the most serious risks. Since tokens carry sensitive information and grant access to protected resources, their exposure can lead to unauthorized access.
Another issue is the revocation problem. Because tokens are stateless, invalidating one before it expires requires additional infrastructure, such as maintaining a token blacklist.
Algorithm confusion attacks are another potential threat, particularly in JWT implementations. Some libraries allow attackers to switch the signing algorithm from asymmetric (e.g., RS256) to symmetric (e.g., HS256), potentially enabling forgery.
To mitigate these risks effectively:
- Use short token lifespans for access tokens, ideally between 15-30 minutes, and pair them with refresh tokens for extended sessions.
- Implement audience restrictions and issuer validation to ensure tokens are used only in their intended contexts.
- Consider using token binding, which cryptographically ties tokens to specific clients or devices.
Token Performance and Scaling Benefits
Tokens’ stateless design eliminates the need for shared session storage, allowing each service to validate requests independently without relying on centralized infrastructure.
This independence translates to improved performance in high-traffic scenarios. Services can validate tokens using cryptographic operations and local configurations, avoiding the latency associated with querying session databases or caches.
Tokens also simplify horizontal scaling. New service instances can immediately process requests without needing access to centralized session storage.
Another advantage is cross-domain functionality. Unlike cookies, which are often restricted to a single domain, tokens can easily be passed between different domains and services.
For globally distributed systems, tokens offer further benefits. Since validation doesn’t require accessing remote session storage, services in different regions can operate independently while maintaining consistent authentication behavior.
Server-Side Session Management
How Server-Side Sessions Work
Server-side session management operates differently from token-based methods by keeping all session data on the server, stored in centralized systems like databases, in-memory stores, or distributed caches.
When a user successfully logs in, the server generates a unique session identifier (session ID), typically a secure random string. The server stores the actual session details — such as user data, permissions, preferences, and application-specific state — on its side. The session ID is then sent to the client, often as a secure HTTP cookie.
Session storage options depend on the application’s needs:
- Simple setups may use in-memory storage, where session data is kept in the server’s RAM.
- More robust systems often rely on dedicated tools like Redis or Memcached.
- Enterprise applications may integrate session data into relational databases.
Server-Side Session Security Benefits
Centralized session control offers several security advantages. One of the most critical is immediate session revocation. If a security issue arises or a user logs out, administrators can instantly invalidate the session by removing it from storage.
By reducing the attack surface on the client side, this method mitigates common vulnerabilities. Unlike tokens stored in browser local storage, server-side sessions limit exposure to the session ID cookie.
Centralized storage also enhances session monitoring and auditing. Security teams can track active sessions, identify unusual patterns, and enforce real-time policies.
Server-Side Session Scaling Problems
Despite their security strengths, server-side sessions face notable scaling challenges due to their reliance on centralized storage. Each request requires a database or cache lookup, which can introduce latency.
Geographic distribution becomes a significant hurdle. Centralized storage increases latency for users far from the server, while distributed storage complicates replication and consistency.
Some organizations are exploring hybrid approaches to balance security and scalability:
- Server-side sessions might be used for sensitive operations, while tokens handle less critical tasks.
- Session caching layers can reduce database load while retaining centralized control.
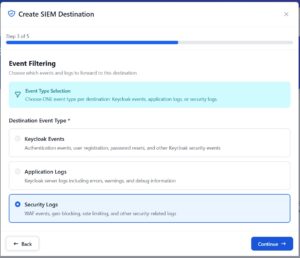
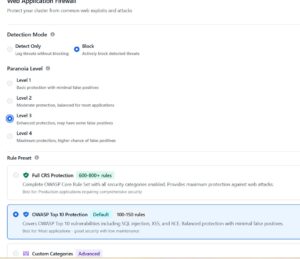
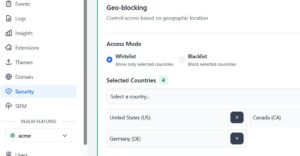
How Keycloak Handles Session Management
Keycloak uses a sophisticated session management system that combines elements of both server-side sessions and tokens. Understanding how Keycloak manages sessions is valuable for any team deploying it in production.
SSO Sessions
When a user authenticates through Keycloak, it creates an SSO Session that tracks the user’s authentication state across all clients in the realm. This session is stored server-side in Keycloak’s Infinispan cache (or a database for persistence). The SSO session enables true single sign-on — once authenticated, the user can access any configured client without re-entering credentials.
Key session settings in the Keycloak Admin Console under Realm Settings > Sessions:
- SSO Session Idle: How long a session can be idle before expiring (default: 30 minutes).
- SSO Session Max: The absolute maximum lifetime of an SSO session (default: 10 hours).
- Client Session Idle / Max: Per-client overrides for session timeouts.
Offline Sessions
Keycloak also supports Offline Sessions for scenarios where applications need long-lived access (e.g., mobile apps that need to work offline). These sessions persist even after the SSO session expires and are tied to offline tokens that can be refreshed independently.
Session Management Features
Keycloak provides several built-in session management capabilities:
- Active session monitoring: View and manage active sessions per user in the Admin Console.
- Session revocation: Administrators can revoke all sessions for a user, a client, or an entire realm instantly.
- Not-before policy: Set a timestamp before which all tokens are considered invalid — useful for emergency revocation.
- Account console: End users can view and terminate their own active sessions.
For production deployments, Skycloak’s managed Keycloak service handles the infrastructure complexity of distributed session storage, ensuring high availability and consistent session behavior across regions.
Cookies vs Tokens vs Server-Side Sessions: Complete Comparison
Side-by-Side Comparison Table
| Aspect | Cookies | Tokens (JWT) | Server-Side Sessions |
|---|---|---|---|
| Security | Prone to CSRF attacks unless mitigated with SameSite and Secure flags | Self-contained but challenging to revoke; vulnerable to XSS if stored in localStorage | Offers strong security with immediate revocation capability |
| Scalability | Limited by server storage; requires sticky sessions or shared storage | Scales well horizontally; built to be stateless | Constrained by centralized storage requirements |
| Performance | Needs a database lookup for every request | Quick validation without server-side storage | Slower due to storage lookups and potential network delays |
| Implementation Complexity | Moderate; demands CSRF protection and secure configurations | Easy to set up initially but revocation can be tricky | Complex for distributed systems |
| Storage Requirements | Relies on server-side storage for session data | No server storage; data is embedded in the token | Needs significant server-side storage and supporting infrastructure |
| Network Overhead | Minimal; transmits only the session ID | Higher due to larger token size (typically 200-1000 bytes) | Minimal; transmits only the session ID |
| Revocation Control | Immediate via server-side deletion | Difficult; involves token blacklists or short expiration times | Immediate and straightforward |
| Cross-Domain Support | Limited; requires careful domain configuration | Excellent; easily shared across multiple services | Needs additional infrastructure for cross-domain setups |
| Compliance Suitability | Works well with most regulations when implemented securely | Can be challenging for strict audit requirements | Ideal for regulatory compliance and audit trails |
How to Choose the Right Method
- Server-side sessions are ideal for secure and regulated environments. They provide instant revocation and detailed audit trails.
- Tokens (JWT) shine in microservices architectures and mobile applications, where stateless authentication and cross-domain compatibility are critical.
- Cookies work well for traditional web applications that require a straightforward approach with balanced security and performance.
A hybrid strategy might be the best fit for many organizations. For example, you could use tokens for API authentication while relying on server-side sessions for high-risk activities.
Best Practices and Common Mistakes
Security Best Practices for Each Method
Cookie-Based Session Management demands careful configuration of security flags. Always set the Secure flag to ensure cookies are transmitted exclusively over HTTPS connections. Use the HttpOnly flag to block JavaScript from accessing cookies. For the SameSite attribute, choose “Strict” for maximum security or “Lax” for a balance between security and usability.
Token-Based Session Management relies on strong cryptographic practices. Use robust algorithms like RS256 or ES256 for signing and encryption, and rotate keys periodically. Keep token payloads minimal to limit exposure if intercepted. Pair short-lived access tokens with a secure refresh mechanism, and validate token signatures and claims on every request.
Server-Side Session Management benefits from centralized control. Encrypt communications between application servers and session storage systems. Design session storage to be highly available and implement automatic cleanup of expired sessions.
Common Implementation Mistakes
- Token expiration gaps: Tokens remain valid until their expiration, even after a user logs out. Minimize token lifespans and implement mechanisms for token revocation.
- Improper cookie configuration: Failing to set critical flags like SameSite, Secure, or HttpOnly leaves cookies vulnerable.
- Sensitive data in tokens: Avoid embedding sensitive information in tokens. JWTs are encoded — not encrypted — and their contents are easily readable if intercepted.
- Session storage misconfigurations: Poorly configured session storage can lead to expired sessions accumulating or persisting longer than needed.
- Cross-domain cookie issues: Misconfiguring cookies for cross-domain scenarios can disrupt authentication across subdomains or related services.
Compliance Requirements for Session Management
- HIPAA compliance: Systems handling protected health information must enforce idle session timeouts, require re-authentication before accessing sensitive data, and maintain detailed audit logs.
- PCI-DSS compliance: Payment processing systems often favor server-side session management for its robust control over session termination.
- GDPR compliance: The GDPR mandates data minimization and secure handling of session data. Organizations must provide users with mechanisms to access and delete session data upon request.
Conclusion
Key Takeaways
Cookies are a strong choice for traditional web applications where simplicity and browser compatibility are key. Tokens are ideal for distributed systems, particularly in microservices or API-driven architectures. Server-side sessions provide centralized control and allow for immediate session revocation, making them well-suited for environments that require strict security.
Implementation Decision Framework
- Security-centric environments: Applications handling sensitive data generally benefit from server-side sessions.
- Scalability demands: Systems expecting rapid growth often lean toward tokens.
- Compliance considerations: Regulatory requirements can heavily influence your choice.
A hybrid approach can often yield the best results. Many organizations use tokens for APIs and server-side sessions for web applications.
Ultimately, your session management strategy should align with your organization’s security priorities, scalability objectives, and operational constraints. For more on Keycloak’s session management capabilities, explore the session management features page and the Skycloak documentation.
FAQs
When should you use a hybrid approach with cookies, tokens, and server-side sessions for session management?
A blended approach can be particularly effective when trying to strike a balance between scalability, security, and flexibility across various application requirements. For example, browser-based session persistence can be efficiently managed using cookies, tokens like JWTs are well-suited for stateless API communication, and server-side sessions are ideal for handling sensitive or high-security data.
How can I ensure compliance with regulations like GDPR and HIPAA when using token-based session management?
To align token-based session management with GDPR and HIPAA requirements:
- Store tokens in secure cookies configured with the
HttpOnlyandSecureflags. - Set short token lifetimes and use refresh tokens.
- Ensure tokens are properly signed and encrypted when necessary.
- Rely on a centralized identity provider to streamline access control and auditing.
- Regularly monitor authentication events and enforce rate limiting.
What are effective strategies for handling scalability challenges with server-side sessions in distributed systems?
Organizations can explore methods that minimize reliance on a single server. One option is externalizing session data to a distributed store like Redis. Another strategy involves adopting stateless authentication through tokens, such as JSON Web Tokens (JWTs). Each solution has its own set of trade-offs, so weigh factors like security, performance, and system complexity to determine the most suitable approach for your architecture.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.