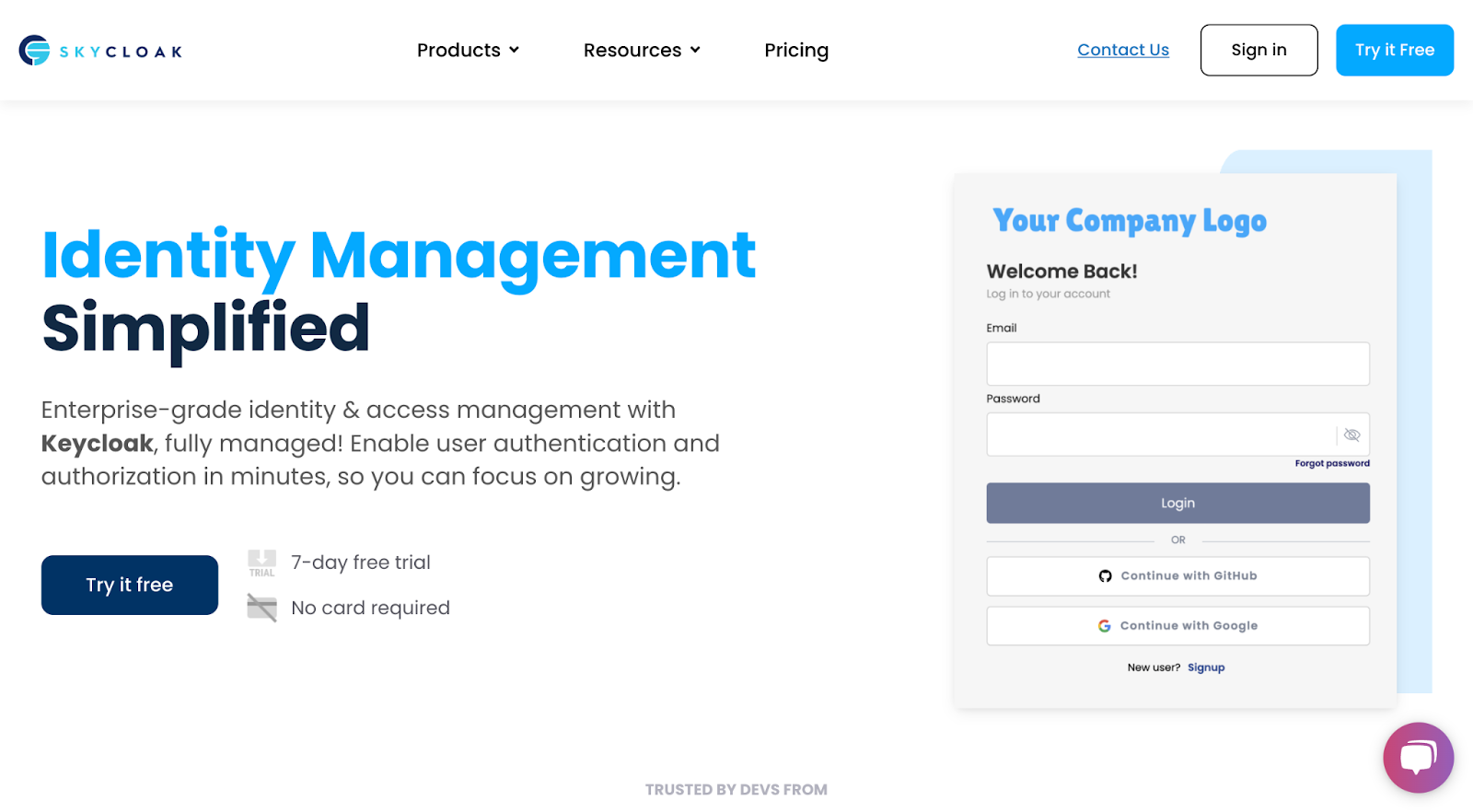
Why Skycloak Is a Premier Choice in the Identity and Access Management Industry
Last updated: March 2026
Identity and access management has become one of the most critical components of modern software architecture. As organizations move to cloud-native environments, the question is no longer whether you need a robust IAM solution — it is which one you can trust to protect your users, your data, and your reputation.
Choosing the wrong provider can mean months of integration work, unpredictable costs, and security gaps that only surface under pressure. Choosing the right one means your team can focus on building your product while identity, authentication, and authorization run reliably in the background.
That is why we built Skycloak: to give engineering teams a remarkable IAM platform that combines the power of open-source Keycloak with the reliability of fully managed infrastructure.
The Rise of Open-Source Identity
The identity management market has grown rapidly alongside broader trends in cybersecurity. As IBM’s Cost of a Data Breach Report highlights, the cost and frequency of security breaches continue to climb year over year. Organizations are responding by investing heavily in identity infrastructure — the first line of defense against unauthorized access.
Within this landscape, Keycloak has emerged as the leading open-source identity and access management platform. Originally developed by Red Hat and now a CNCF incubating project, Keycloak provides a comprehensive feature set that rivals proprietary solutions: single sign-on, identity brokering, user federation, fine-grained authorization, and standards-based protocol support for OpenID Connect, OAuth 2.0, and SAML 2.0.
What makes Keycloak remarkable is its flexibility. Unlike closed-source IAM vendors that lock you into their ecosystem, Keycloak gives you full control over your identity infrastructure. You own your data, your configuration, and your user base. There is no vendor lock-in, no per-user pricing that punishes growth, and no artificial feature gates.
But Keycloak’s power comes with a tradeoff: operational complexity. Running Keycloak in production — with high availability, automatic updates, monitoring, backups, and security hardening — requires significant DevOps expertise and ongoing maintenance. That operational burden is exactly what Skycloak eliminates.
What Makes Skycloak Different
Skycloak is a fully managed Keycloak hosting platform purpose-built for teams that want the capabilities of Keycloak without the infrastructure overhead.
When you deploy a Keycloak instance through Skycloak, you get a production-ready environment in minutes — not weeks. Every instance includes:
- High availability architecture with automated failover, so your authentication layer stays up even during infrastructure incidents.
- Automatic updates and patching that keep your Keycloak version current with the latest security fixes, without requiring your team to plan and execute upgrade cycles.
- Automated backups with point-in-time recovery, protecting your identity data against accidental loss or corruption.
- Performance monitoring and alerting so you know about issues before your users do.
- SOC 2 compliant infrastructure that meets the security and compliance requirements of enterprise customers.
Self-hosting Keycloak means your engineering team becomes responsible for database tuning, TLS certificate management, JVM optimization, clustering configuration, and a dozen other operational concerns. With Skycloak, all of that is handled for you by a team that specializes in running Keycloak at scale.
Enterprise-Grade Features Out of the Box
Skycloak gives you access to the full breadth of Keycloak’s identity capabilities, enhanced with management tooling that makes configuration and monitoring straightforward.
Single Sign-On and Identity Federation
Single sign-on is the foundation of modern identity. Skycloak supports SSO across all your applications using OpenID Connect, OAuth 2.0, and SAML 2.0. Users authenticate once and gain access to every connected service — reducing password fatigue and improving security posture.
You can also connect external identity providers including Google, Microsoft, GitHub, Apple, and any standards-compliant SAML or OIDC provider. This makes it simple to support social login, enterprise federation, and B2B identity brokering from a single platform.
Multi-Factor Authentication
Passwords alone are not enough. Skycloak supports multi-factor authentication with TOTP authenticator apps, WebAuthn/FIDO2 security keys, and SMS-based verification. You can enforce MFA policies globally or on a per-application basis, and configure adaptive authentication flows that challenge users based on risk signals.
Role-Based Access Control
Fine-grained role-based access control lets you define exactly who can access what. Skycloak supports realm roles, client roles, composite roles, and group-based policies. You can model complex authorization hierarchies — from simple admin/user distinctions to multi-tenant permission structures.
Audit Logs and Compliance
Every authentication event, admin action, and configuration change is recorded in detailed audit logs. These logs are essential for compliance requirements like SOC 2, HIPAA, and GDPR, and they give your security team visibility into who accessed what and when.
User and Team Management
The Skycloak dashboard provides intuitive user management capabilities — create users, manage attributes, reset credentials, and view session activity. For organizations with multiple administrators, team management features let you delegate responsibilities with appropriate access controls.
Security as a Foundation
Security is not a feature we bolt on — it is the foundation everything else is built on. As the Verizon Data Breach Investigations Report demonstrates, organizations face an expanding threat landscape that demands robust identity infrastructure.
Skycloak takes a defense-in-depth approach to security:
- Encryption at rest and in transit for all identity data, using industry-standard TLS 1.3 and AES-256 encryption.
- Network isolation with dedicated infrastructure that keeps your identity data separate from other tenants.
- Session management with configurable timeouts, concurrent session limits, and the ability to revoke sessions in real time.
- Brute-force protection with automatic account lockout policies and IP-based rate limiting.
- Regular penetration testing and vulnerability assessments conducted by third-party security firms.
Our infrastructure runs on SOC 2 compliant systems, and we maintain security practices that meet the requirements of healthcare, financial services, and government organizations.
Built for Developers
We believe that a great IAM platform should be easy to integrate, well-documented, and supported by tools that accelerate development.
Comprehensive Documentation
Our documentation covers everything from initial setup to advanced configuration — realm management, client registration, authentication flows, identity brokering, and API integration. Whether you are connecting your first application or implementing a complex multi-tenant architecture, the docs provide clear, step-by-step guidance.
Developer Tools
Skycloak provides a suite of free developer tools to streamline your identity workflow:
- JWT Token Analyzer — Decode and inspect JSON Web Tokens to debug authentication issues.
- SAML Decoder — Parse and validate SAML assertions for enterprise SSO integrations.
- Keycloak Config Generator — Generate Keycloak configuration files for common deployment patterns.
- Docker Compose Generator — Create Docker Compose files for local Keycloak development environments.
- SCIM Endpoint Tester — Test SCIM provisioning endpoints for automated user lifecycle management.
These tools work standalone — you do not need a Skycloak account to use them.
Standards-Based APIs
Because Skycloak is built on Keycloak, you get full access to Keycloak’s Admin REST API. Every operation you can perform in the UI is also available via API, making it straightforward to automate user provisioning, client registration, and realm configuration as part of your CI/CD pipeline.
Integration is similarly straightforward. Keycloak’s standards-based approach means any library that supports OpenID Connect or SAML will work with Skycloak — no proprietary SDKs required.
Cost Efficiency That Scales
IAM pricing models vary widely, and many organizations discover too late that per-user pricing from vendors like Auth0 or Okta becomes prohibitively expensive as their user base grows.
Skycloak takes a different approach. Our pricing is based on infrastructure capacity, not user count. Whether you have 1,000 users or 1,000,000, you pay for the compute and storage resources your instance needs — not a per-seat tax on every user in your directory.
Consider the alternatives:
- Self-hosting Keycloak requires dedicated DevOps resources for setup, maintenance, upgrades, monitoring, and incident response. For most teams, the fully loaded cost of an engineer spending 20-30% of their time on Keycloak operations exceeds the cost of a managed solution.
- Proprietary IAM vendors like Auth0 and Okta charge per monthly active user, with enterprise features locked behind higher pricing tiers. At scale, these costs can reach tens of thousands of dollars per month — and you are locked into their platform with no data portability guarantees.
- Skycloak gives you predictable, capacity-based pricing with full access to every Keycloak feature. No per-user fees, no feature gates, and no lock-in. Your identity data is always yours to export.
Growing with Your Business
Identity requirements evolve as your organization grows. Skycloak is designed to scale alongside your business without requiring architectural changes.
Multi-Realm Architecture
Keycloak’s realm model lets you isolate identity configurations for different applications, environments, or tenants. Skycloak makes it easy to manage multiple realms from a single dashboard — spin up new realms for staging environments, create isolated identity boundaries for B2B customers, or separate internal and external user populations.
Custom Domains
Your authentication pages should feel like part of your product, not a redirect to a third-party service. Skycloak supports custom domains so your login, registration, and account management pages live on your own domain with your own branding.
Theme and Branding Customization
With Skycloak’s branding capabilities and theme library, you can customize the look and feel of every user-facing page. Match your authentication experience to your product design without writing custom Keycloak themes from scratch.
Extensions and Integrations
Keycloak’s extension model supports custom authentication flows, event listeners, and protocol mappers. Skycloak supports deploying extensions to your managed instance, so you get the customizability of self-hosted Keycloak with the reliability of managed infrastructure.
Conclusion
The identity and access management landscape is crowded, but the choice becomes clear when you evaluate what actually matters: security, reliability, developer experience, and cost predictability.
Skycloak delivers the full power of Keycloak — the most capable open-source IAM platform available — without the operational burden of self-hosting. You get enterprise-grade features, SOC 2 compliant infrastructure, comprehensive documentation, and pricing that does not punish you for growing your user base.
If you are evaluating IAM solutions for your organization, start with Skycloak. Deploy a production-ready Keycloak instance in minutes and see the difference that managed identity infrastructure makes.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.

