Keycloak Auditing: Best Practices for Security
Last updated: March 2026
In a previous blog post, we looked at what is auditing in Keycloak and how it could be implemented. Today, we will take a look at the best practices on implementing a good auditing system.
Centralize Log Management
For organizations managing multiple systems, it’s crucial to centralize log management. This involves integrating Keycloak’s audit logs with a centralized log management solution such as ELK (Elasticsearch, Logstash, and Kibana) or Splunk. This approach offers several benefits:
- Unified View: Consolidate logs from various sources for a holistic view of security-related activities across all platforms.
- Enhanced Analysis: Utilize advanced tools for log analysis to detect patterns, anomalies, or potential security threats more effectively.
- Real-Time Monitoring: Set up real-time alerts based on specific events or thresholds to enable immediate responses to potential security incidents.
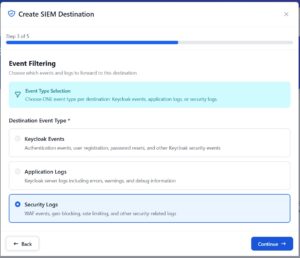
Configuring Keycloak Event Listeners
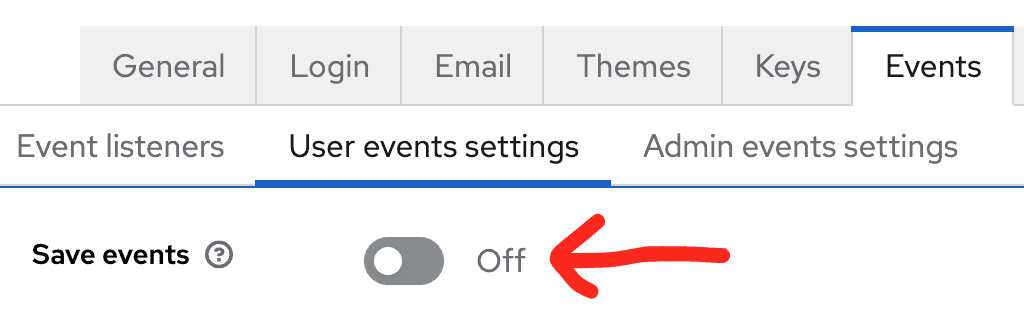
Keycloak uses Event Listener SPIs to process and forward events. To configure event listeners in the Admin Console:
- Navigate to Realm Settings > Events > Config.
- Enable Save Events for both Login Events and Admin Events.
- Under Event Listeners, you can add custom event listeners beyond the default
jboss-logging.
Keycloak captures two categories of events:
- Login Events: User authentication attempts, logouts, token refreshes, code-to-token exchanges, and registration events.
- Admin Events: Configuration changes to realms, clients, roles, users, and other administrative actions.
For forwarding events to external systems, consider using Skycloak’s built-in Event Viewer, which provides a managed UI for browsing and filtering events without needing to set up a separate logging pipeline. You can also forward events using:
- HTTP Webhook: Push events to any HTTP endpoint in real-time. See our guide on forwarding Keycloak events to SIEM via HTTP webhook.
- Syslog: Forward events using the standard syslog protocol for integration with traditional SIEM systems. See integrating security logs using syslog.
For monitoring dashboards and real-time event analysis, Skycloak provides built-in insights and analytics that visualize authentication patterns and alert on anomalies.
Retain Audit Logs for Compliance
Different industries and jurisdictions have specific requirements for how long audit logs must be retained. Ensure compliance with these regulations by setting up policies within your log management system to retain logs for the required duration. For example:
- Healthcare (HIPAA): Requires six years of log retention.
- Financial Services (GLBA, SOX): Requires log retention ranging from three to seven years depending on the specific regulation.
Retaining the events in Keycloak for extended periods could impact performance if running for a high number of active users. Instead, forward events to an external system with proper retention policies and archive older events to cold storage.
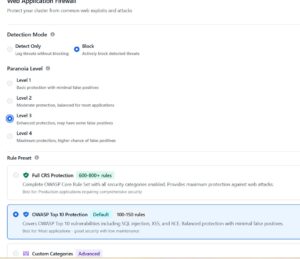
Secure and Encrypt Auditing Log Data
Since audit logs can contain sensitive information, securing these logs is paramount. Apply encryption both in transit and at rest to protect log data from unauthorized access. Additionally, manage access controls strictly to ensure that only authorized personnel can view or manipulate the logs.
Key considerations for log security:
- Encrypt in transit: Use TLS for all log transport (syslog over TLS, HTTPS for webhook endpoints).
- Encrypt at rest: Enable encryption on your log storage backend (e.g., encrypted S3 buckets, encrypted Elasticsearch indices).
- Access controls: Implement role-based access to log data. Not every team member needs access to raw authentication events.
- Integrity protection: Consider log signing or write-once storage to prevent tampering with historical log data.
Regular Auditing and Reviews
Schedule regular audits of your audit logs to ensure that logging mechanisms are working as expected and that no unauthorized changes have been made to the logging configurations. Regular reviews can help in:
- Verifying the Integrity of Logs: Ensure that logs are complete, accurate, and free of tampering.
- Assessing the Efficacy of Log Policies: Evaluate if current logging policies are effective in capturing relevant data and meeting compliance requirements.
- Optimizing Log Storage: Adjust storage solutions based on log volume and retention requirements to manage costs and performance.
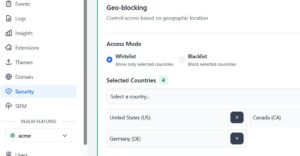
Automated Notifications
Configure automated responses to specific types of log events that may indicate critical security incidents. For example, if multiple failed login attempts are logged, an alert system could send a notification to an administrator. This proactive approach enhances security by reducing the response time to potential threats. It also allows the business to determine how reliable the business is periodically.
Examples of events that should trigger alerts:
- Brute force detection: Multiple failed login attempts from the same IP or for the same user within a short time window.
- Admin configuration changes: Any changes to realm settings, client configurations, or authentication flows in production.
- Unusual token activity: Spikes in token refresh requests or token validation failures.
- New admin user creation: Any new user being granted admin privileges.
Implementing Audit Log Best Practices with Keycloak
To put these best practices into action within your Keycloak setup:
- Configure External Logging: Use Keycloak’s Event Listener SPI to integrate with an external log management solution of your choice. For a managed approach, Skycloak’s built-in event forwarding handles this automatically.
- Establish Log Retention Policies: Set up your external log management tool to automatically archive and purge logs according to your industry’s compliance requirements.
- Encrypt and Secure Logs: Ensure that your log management solution supports encryption and manage access with role-based access controls.
- Schedule Regular Reviews: Set calendar reminders for periodic log audits and adjust your audit strategy based on findings from these reviews.
- Set Up Alerts and Automations: Utilize features in your log management system to create alerts and automations that respond to specific logging events.
Conclusion
By following these best practices, you can maximize the benefits of Keycloak’s auditing capabilities, enhancing your organization’s security posture and ensuring compliance with relevant regulations.
For a complete overview of how auditing works in Keycloak, revisit our guide on auditing in Keycloak: how to catch them all. To explore Skycloak’s managed auditing and monitoring capabilities, check out the audit logs feature page and the insights dashboard.
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.