authorization
Articles tagged with authorization.
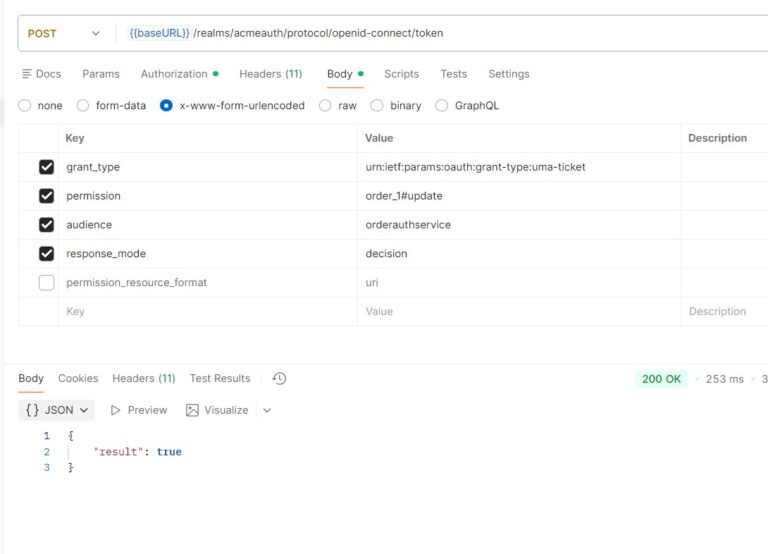
Fine-Grained Authorization in Keycloak Explained
Understand how Keycloak fine-grained authorization works using UMA policies, scopes, and RPT or JSON-based decisions for secure resource access control.

Keycloak ABAC Configuration: Step-by-Step Guide
Learn how to configure Attribute-Based Access Control (ABAC) in Keycloak with this step-by-step guide covering policies, resources, and permissions.
Supabase or Keycloak? A Complete Guide
Compare Supabase and Keycloak for authentication and authorization. Learn when to use each, how to connect them together, and which…
Understanding Application Authorization: A Very Small Guide
Unlock the secrets of digital security with our comprehensive guide to authorization. Learn how to protect your application and users…
Implementing RBAC in Keycloak: Roles, Scopes, and Policies
Learn how to implement RBAC in Keycloak with realm roles, client roles, policies, and JWT token mapping for secure authorization.
OAuth 2.1: What Changed and How Keycloak Implements It
Discover OAuth 2.1 changes including mandatory PKCE, deprecated implicit flow, and how Keycloak implements these security improvements since version 24.
Choosing the Best Authorization Flows for Your App
Understand and recognize the current OAuth and OIDC Authorization flows to secure your frontend applications effectively
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.