Okta vs Keycloak: Policies vs Authentication Flows Details

Introduction
When working with modern IAM platforms like Okta and Keycloak, one subtle but critical difference lies in how authentication logic is modeled and enforced.
At first glance, both support MFA, conditional access, and strong authentication. But under the hood, they take fundamentally different approaches.
Core Philosophy
Okta → Policy-driven (declarative)
Keycloak → Flow-driven (procedural)
This distinction explains many real-world behaviors—especially around MFA failures and fallback handling.
Okta distributes authentication across multiple policy layers
Keycloak centralizes authentication inside flows
Okta = Layered Gates:
Gate 1 → Can you log in? (Global Policy)
Gate 2 → Can you access app? (App Policy)
Gate 3 → Do you have required factors? (Enrollment)Each gate must pass independently.
If any gate fails → ❌ Access denied.
Keycloak = Single Pipeline:
Keycloak centralizes authentication into a single flow pipeline:
Step 1 → Identify user
Step 2 → Authenticate
Step 3 → Enforce MFA
Step 4 → Apply conditions
Step 5 → Issue tokenEverything happens in one controlled execution path.
Keycloak: Flow-Based Authentication
In Keycloak, authentication is modeled as a sequence of execution steps (flows).
Each step has a requirement:
- REQUIRED → Must pass
- ALTERNATIVE → Any one can pass
- DISABLED → Disabled
- CONDITIONAL → Executed based on logic
For more details on Keycloak Authentication Flows, please refer the server admin guide available here.
Key Behaviour
- Built-in fallback via ALTERNATIVE
- Multiple paths to success
- Much more flexible for real-world scenarios
Real-World Scenario Comparison
Requirement
External users accessing an application must use MFA, preferably phishing-resistant.
Okta Approach
- Implemented using App Sign-On Policy
- Condition:
- IF Group = External
- Action:
- Require Password + MFA (e.g., FastPass)
📌 Important behavior:
- First matching rule is enforced
- No fallback between rules
- If required authenticator is unavailable → ❌ Access denied
Okta Policy Evaluation (Diagram)
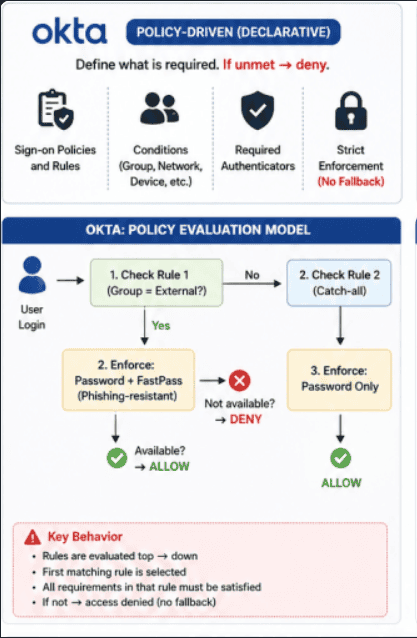
Note: For simplicity, only App-level policy is shown above. In reality, Okta evaluates multiple policy layers.
Okta Layered Architecture vs Keycloak Flow
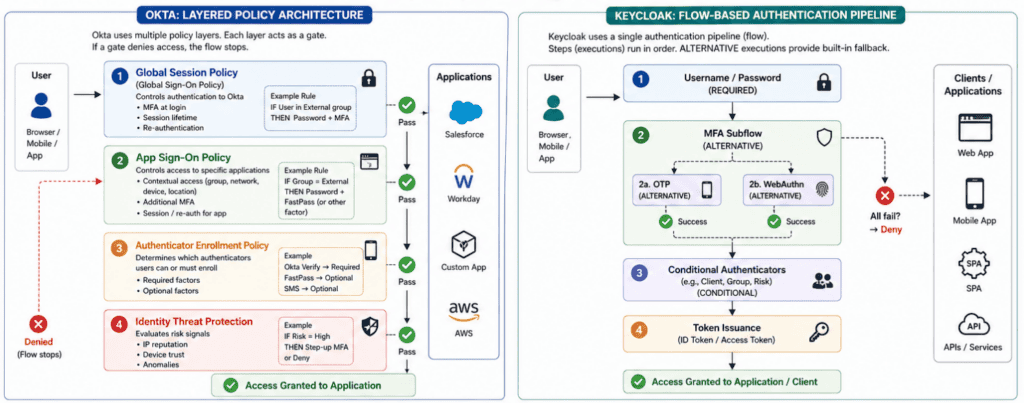
Note: Keycloak for specific access use a single authentication flow. But this authentication flow can be different for different client applications.
Skycloak, the managed Keycloak, has options to enhance security like configurable WAF, Geo-Blocking, IP Access Control etc.
Keycloak Approach
Keycloak achieves the same requirement using conditional authentication flows.
Since group-based conditions may not always be available, we can use roles.
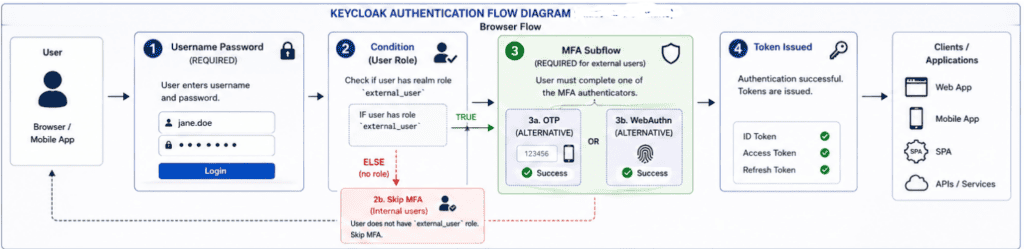
Logic
IF user has role "external_user"
→ Enforce MFA
ELSE
→ Skip MFAOutcome
- External users → MFA enforced
- Internal users → Password only
- Fallback available via ALTERNATIVE executions
Key Insight
Keycloak does not use policies like Okta.
Instead, authentication flows + conditions (role, IdP, client) provide equivalent control—often with greater flexibility
Summary
In this blog, we explored:
- Okta’s layered policy model
- Keycloak’s flow-based authentication
- How both handle MFA and conditional access differently
About Skycloak
Skycloak is a fully managed Keycloak platform hosted in the cloud. It enables organizations to leverage the power of open-source Keycloak IAM without the operational overhead of installing, maintaining, and scaling production-grade Keycloak environments — delivered securely and cost-effectively.
If you’re new to Skycloak, visit the Skycloak Getting Started Guide to learn more
Ready to simplify your authentication?
Deploy production-ready Keycloak in minutes. Unlimited users, flat pricing, no SSO tax.