keycloak
Articles tagged with keycloak.
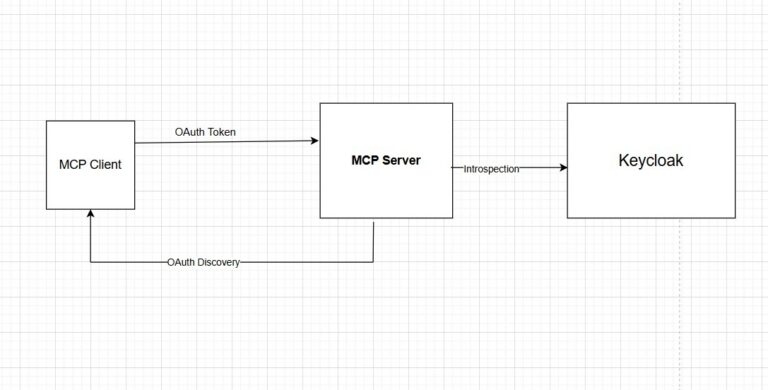
Securing MCP Servers with Keycloak OAuth 2.0
Learn how to secure Model Context Protocol (MCP) servers using Keycloak OAuth 2.0 with token introspection, audience validation, and RFC…
From Loki to ClickHouse: Scaling Our Log Analytics Infrastructure
A technical deep-dive into why we migrated from Grafana Loki to ClickHouse for Keycloak log storage and analytics, including cardinality…
IoT Identity Management: Securing Connected Devices with Keycloak
Learn how to implement IoT identity management with Keycloak. This guide covers OAuth 2.0 Device Authorization Grant, machine-to-machine authentication, Zero…
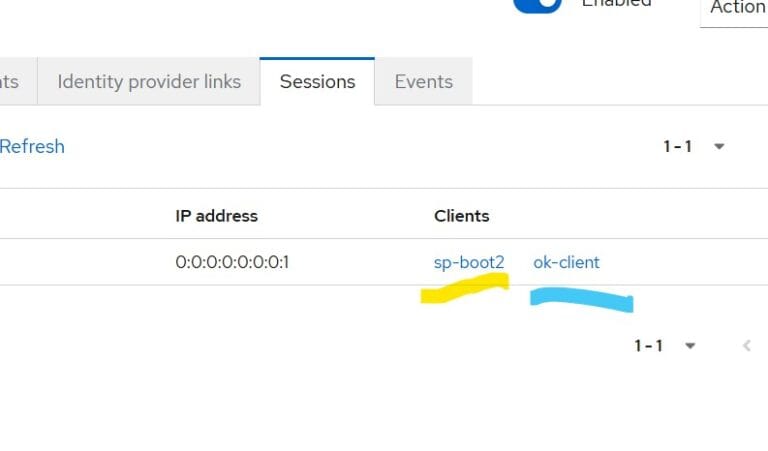
Migrating from Legacy Keycloak Spring Boot Adapters
Step-by-step guide to migrating from deprecated Keycloak Spring Boot adapters to Spring Security native OAuth2/OIDC support in your Java applications.
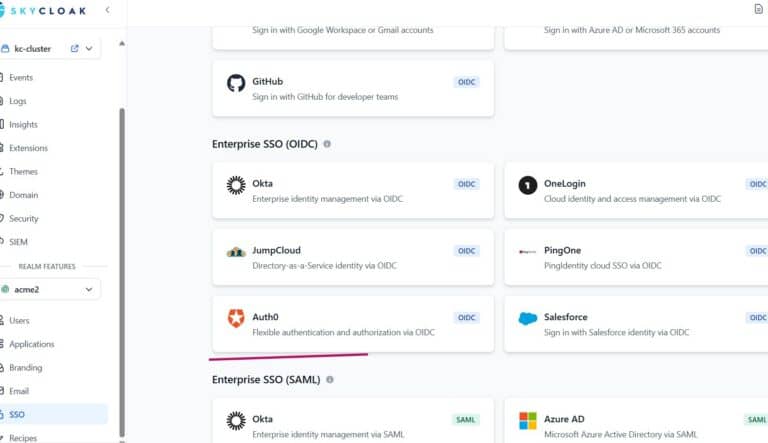
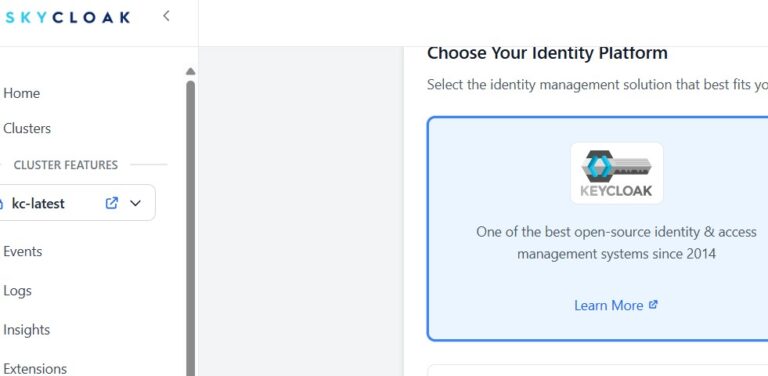
Integrating Keycloak with Auth0 Using Skycloak SSO Templates
Learn how to integrate Keycloak with Auth0 using Skycloak SSO templates. Step-by-step OIDC identity brokering tutorial with mapper configuration.
How to Configure Microsoft Entra ID as a SAML Identity Provider in Keycloak
Step-by-step guide to configuring Microsoft Entra ID as a SAML identity provider in Keycloak, with attribute mappers, metadata import, and…
Bridging IdP-Initiated SAML to OIDC with Keycloak
Learn how to use Keycloak as a protocol bridge between legacy SAML IdPs using IdP-initiated SSO and modern OIDC applications.

Top 7 Keycloak Cluster Configuration Best Practices
Learn the top 7 Keycloak cluster configuration best practices covering discovery, Infinispan caching, database pooling, sticky sessions, and monitoring.
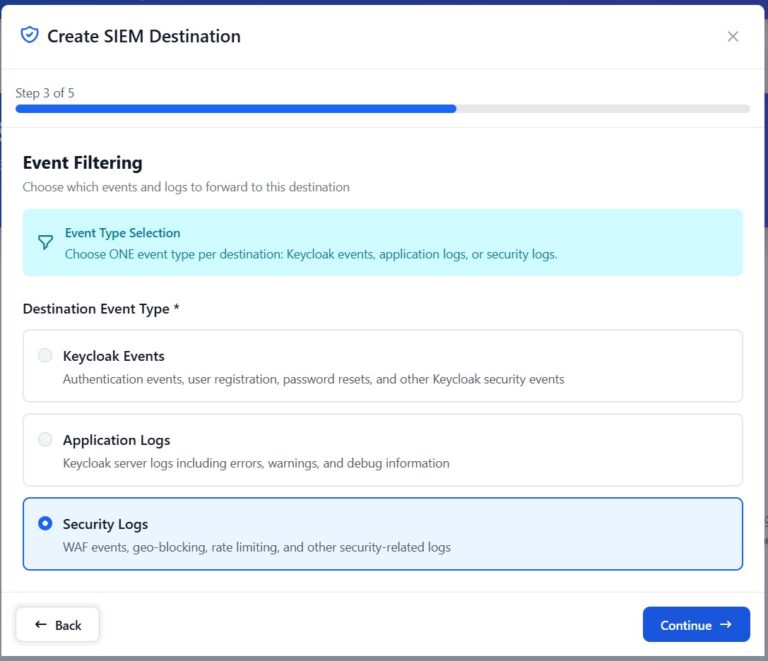
Integrating Skycloak Security Logs Using Syslog
Learn how to forward Skycloak security logs to external SIEM platforms via syslog for centralized monitoring, alerting, and compliance.
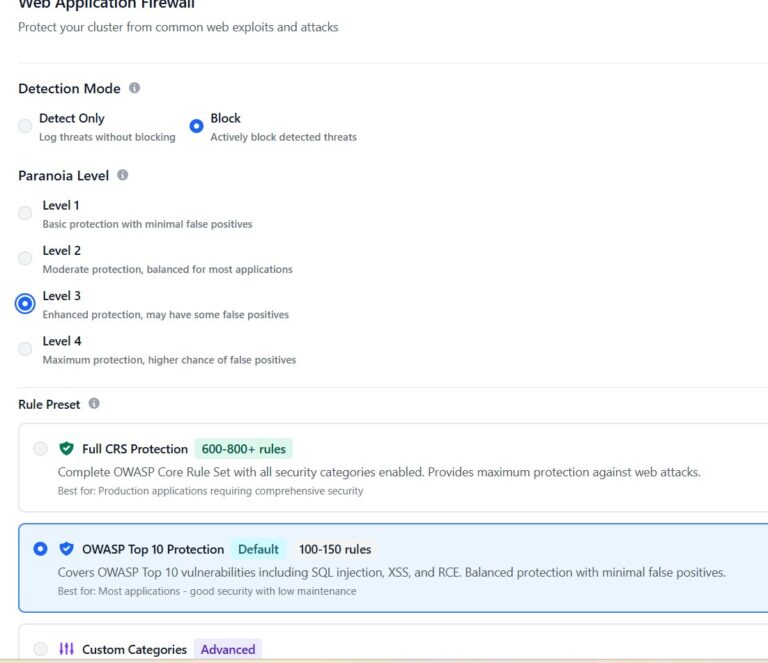
Securing Keycloak with Skycloak’s Configurable WAF
Learn how to configure Skycloak's built-in WAF to protect your Keycloak deployment from brute force attacks, credential stuffing, and DDoS…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.