security
Articles about security from the Skycloak team.
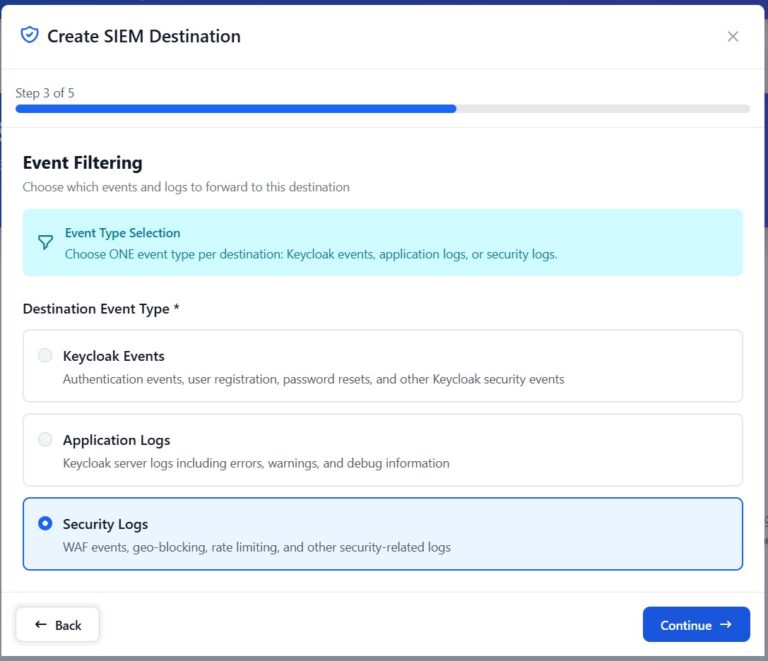
Integrating Skycloak Security Logs Using Syslog
Learn how to forward Skycloak security logs to external SIEM platforms via syslog for centralized monitoring, alerting, and compliance.
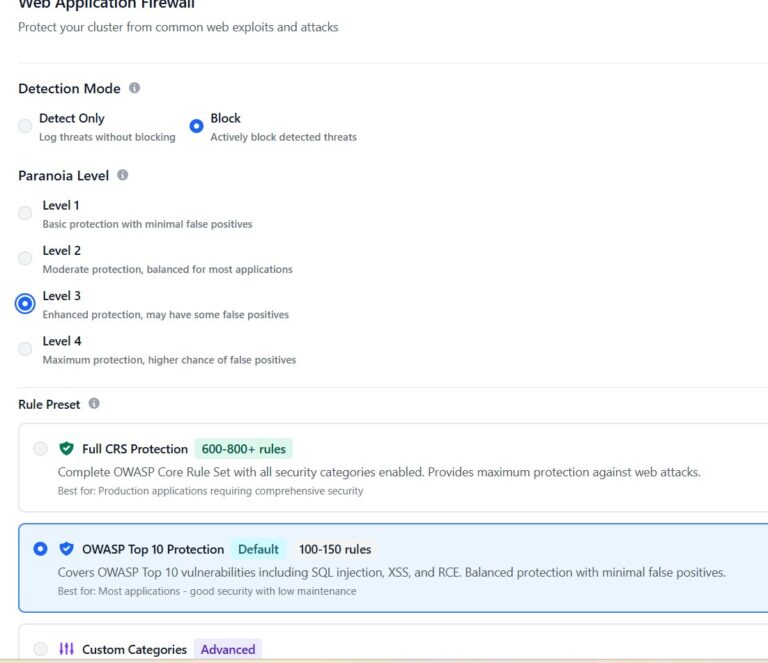
Securing Keycloak with Skycloak’s Configurable WAF
Learn how to configure Skycloak's built-in WAF to protect your Keycloak deployment from brute force attacks, credential stuffing, and DDoS…
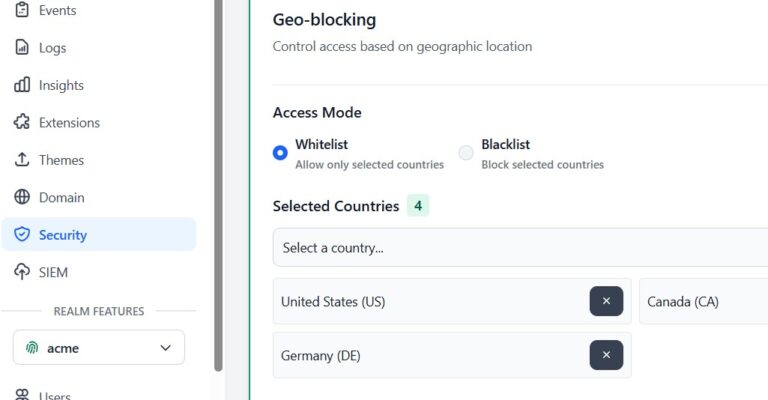
Geo-Blocking Your Keycloak Cluster Using Skycloak
Learn how to restrict access to your Keycloak cluster by country using Skycloak's built-in geo-blocking, reducing attack surface and meeting…
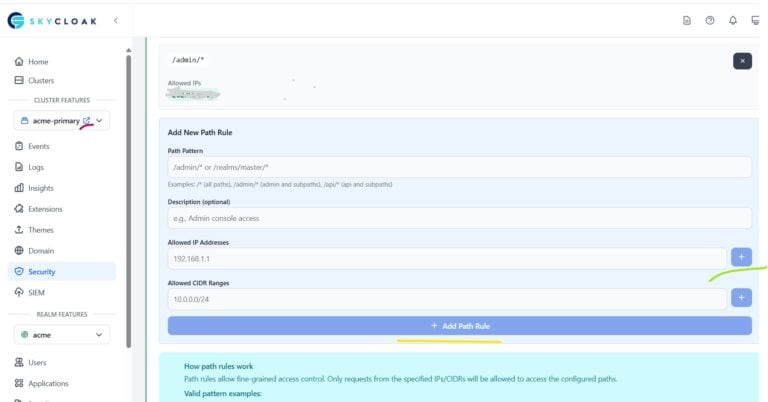
Path-Based IP Restriction for Keycloak Admin Console
Restrict Keycloak admin console access using IP and CIDR-based whitelisting on Skycloak to secure the /admin/* path from unauthorized access.

Session Management in Distributed Systems: Cookies vs Tokens vs Server-Side Sessions
Compare cookies, tokens, and server-side sessions for distributed systems with security analysis, scalability trade-offs, and Keycloak session management.

JWT Token Lifecycle Management: Expiration, Refresh, and Revocation Strategies
Learn JWT token lifecycle management strategies including expiration policies, refresh token rotation, and revocation mechanisms for secure authentication systems.

Keycloak ABAC Configuration: Step-by-Step Guide
Learn how to configure Attribute-Based Access Control (ABAC) in Keycloak with this step-by-step guide covering policies, resources, and permissions.
Keycloak SAML Security: Common Vulnerabilities and How to Harden Your Configuration
Explore Keycloak SAML security vulnerabilities including CVE-2024-8698, XML wrapping attacks, and assertion replay, with hardening steps.

Keycloak vs Okta: Enterprise IAM Comparison Guide
Compare Keycloak and Okta for enterprise IAM including deployment options, MFA, integrations, compliance certifications, and total cost of ownership.

Reducing Insider Risk with IAM Security Measures
Learn how to reduce insider risk with IAM security measures in Keycloak, including RBAC, MFA, audit logging, and zero trust…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.