Insights on Identity, Security & Keycloak
Tutorials, deep dives, and best practices from the Skycloak team.
Why Skycloak Is a Premier Choice in the Identity and Access Management Industry
Discover why Skycloak IAM managed Keycloak hosting delivers enterprise-grade identity management without the operational burden of self-hosting.

Reducing Insider Risk with IAM Security Measures
Learn how to reduce insider risk with IAM security measures in Keycloak, including RBAC, MFA, audit logging, and zero trust…
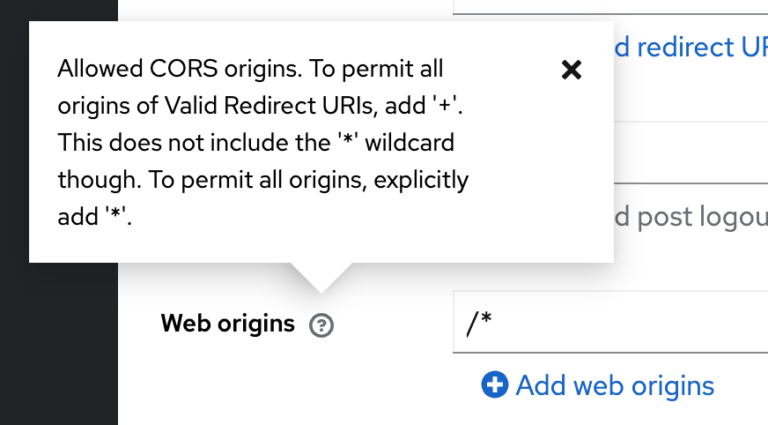
Configuring CORS with Your Keycloak OIDC Client
Learn how to configure CORS for Keycloak OIDC clients, fix common cross-origin errors, and secure browser-based apps with proper Web…
Supabase or Keycloak? A Complete Guide
Compare Supabase and Keycloak for authentication and authorization. Learn when to use each, how to connect them together, and which…
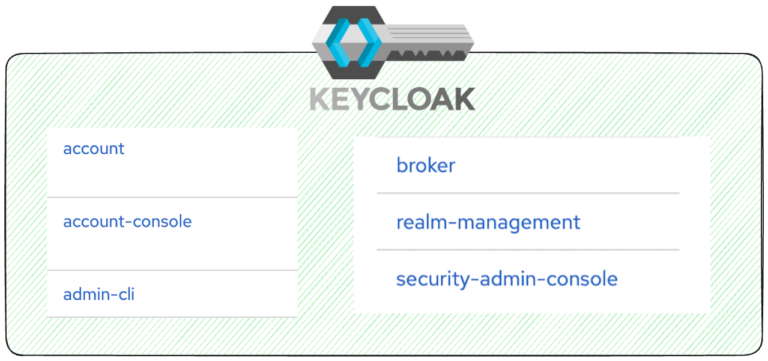
What to Do With the Default Clients in Your Newly Created Keycloak Realm?
Learn what each default Keycloak realm client does and how to harden security by disabling unused clients and reviewing scopes.

What is Keycloak Quarkus and Why You Need it Now Instead of WildFly?
Keycloak evolves, and the shift to Quarkus was a game-changer. Discover why you should be considering this move for your…

8 Default Configurations to Adjust Right Away on Your Keycloak Cluster
Optimize your Keycloak cluster by adjusting these 8 critical default configurations for database, HTTPS, email, sessions, grants, admin security, and…

6 Key Security Insights For You To Understand Access Enforcement
Six crucial security insights that will help you understand and implement useful access enforcement in your organization.

Top 5 Access Control Solutions You Must Know to Fortify Application Security
Discover essential access control solutions to protect your digital assets. Dive deep into simple analysis and comparisons.

6 Key Security Insights For You To Understand Access Enforcement
Understand better access enforcement with these six key security insights. Improve your digital protection now!
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.