keycloak
Articles tagged with keycloak.

Top Auth0 Alternatives in 2026: Open Source and Managed Options
Compare the best Auth0 alternatives in 2026 including Keycloak, FusionAuth, SuperTokens, Clerk, Ory, and Zitadel with pricing, features, and trade-offs.

Add Authentication to Your Next.js App with Keycloak
Complete guide to integrating Keycloak with Next.js 14+ App Router using Auth.js v5. Covers SSO, token refresh, role-based access, and…
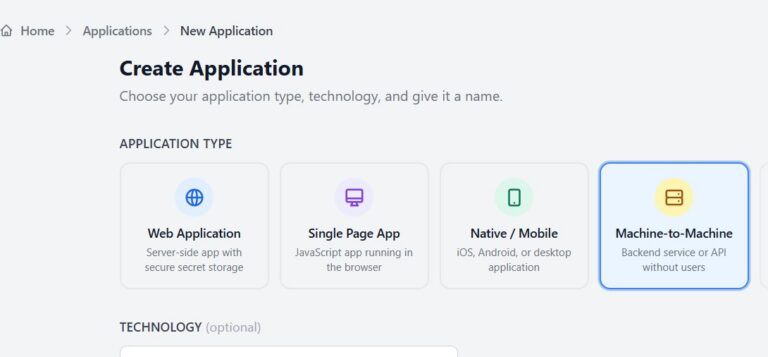
Client Credentials Flow with Skycloak and Node.js
Learn Client Credentials flow using Skycloak and Node.js. Implement secure machine-to-machine authentication with practical examples.

Identity Governance Workflows: Building Automated Access Request and Approval with Keycloak
Build automated access request and approval workflows with Keycloak using custom required actions, the Admin REST API, and group-based access…

Integrating Keycloak with Angular: A Complete Guide
Step-by-step tutorial for integrating Keycloak authentication with Angular 17+ using standalone components, route guards, token interceptors, and role-based access.

Authentication Error Handling in Keycloak: Customizing Error Pages and User Experience
Learn how to customize Keycloak error pages, handle OAuth/OIDC errors in your app, and configure brute force protection for secure,…

Monitoring Keycloak with Prometheus and Grafana
Learn how to monitor Keycloak with Prometheus and Grafana. Enable metrics, track authentication KPIs, build dashboards, and define SLOs for…

Configuring MFA in Keycloak: Enterprise Patterns
A practical guide to configuring MFA in Keycloak, covering OTP policies, WebAuthn, conditional flows, client-specific overrides, and token-based MFA detection.
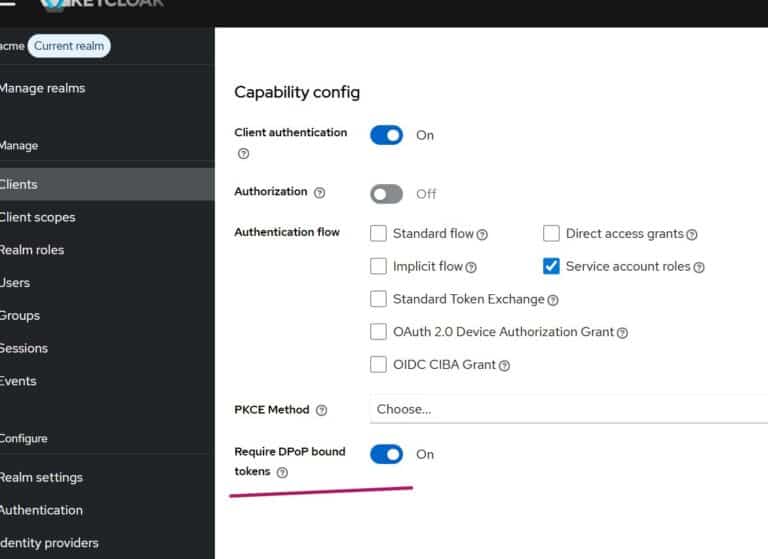
DPoP with Keycloak Admin API Using Node.js
Implement DPoP proof-of-possession tokens with Keycloak Admin API using Node.js to prevent token replay attacks and secure API access.
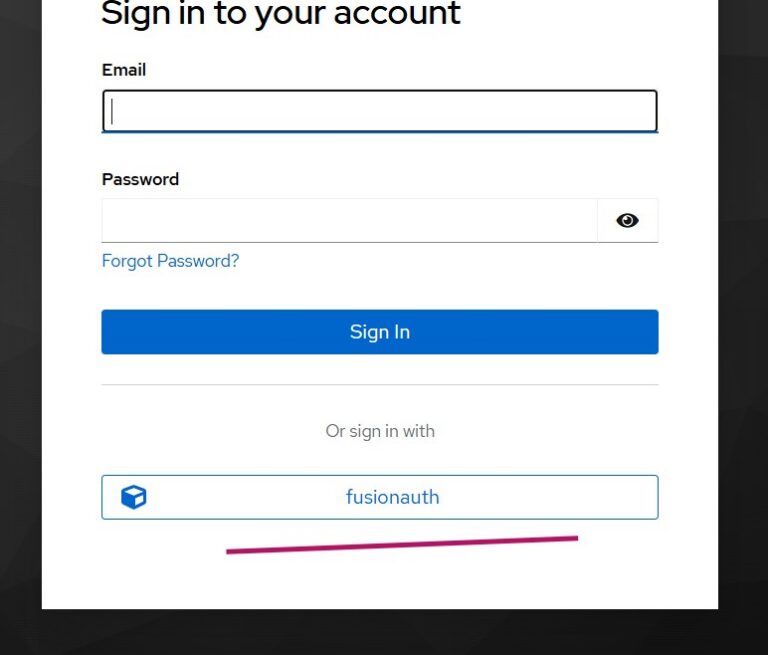
Keycloak Identity Brokering with FusionAuth
Learn how to configure Keycloak as an identity broker with FusionAuth using OIDC, enabling federated authentication and seamless user migration.
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.