keycloak
Articles tagged with keycloak.
Authentication Technology Refresh: Modernization Planning and Timeline
Plan your authentication modernization with this step-by-step guide covering protocol selection, migration timelines, and compliance requirements.

Identity Service Procurement: Contract Negotiation and SLA Requirements
Navigate IAM procurement with essential contract negotiation strategies, SLA benchmarks, compliance requirements, and vendor evaluation best practices.
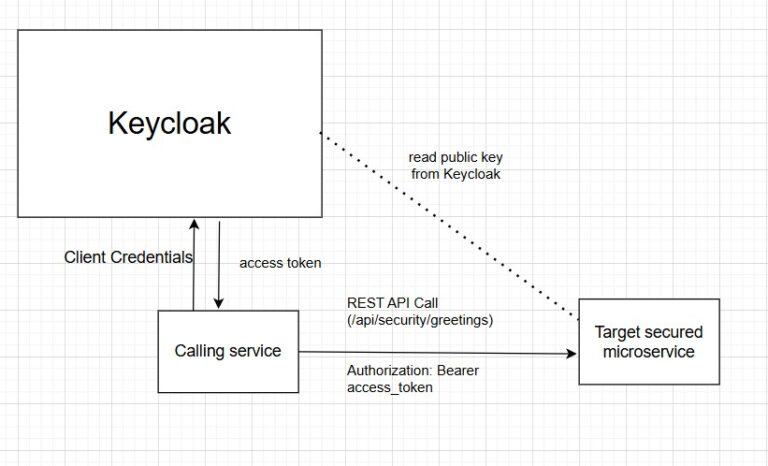
Secure Your Spring Boot REST API with Keycloak Token
Secure your Spring Boot REST API using Keycloak Client Credentials Grant with OAuth2 Resource Server and role-based access control.
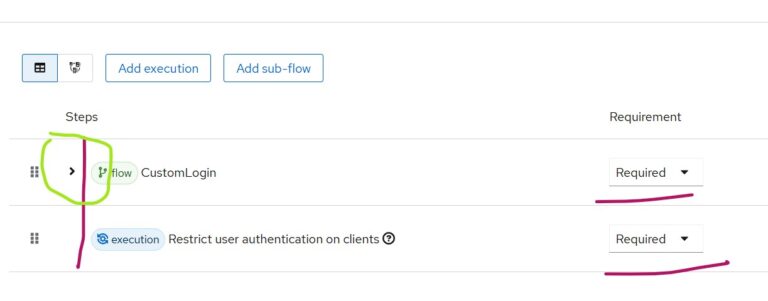
Restrict Keycloak Clients to Specific Users
Learn how to restrict Keycloak client access to specific users using client roles, custom authentication flows, and group-based access control.
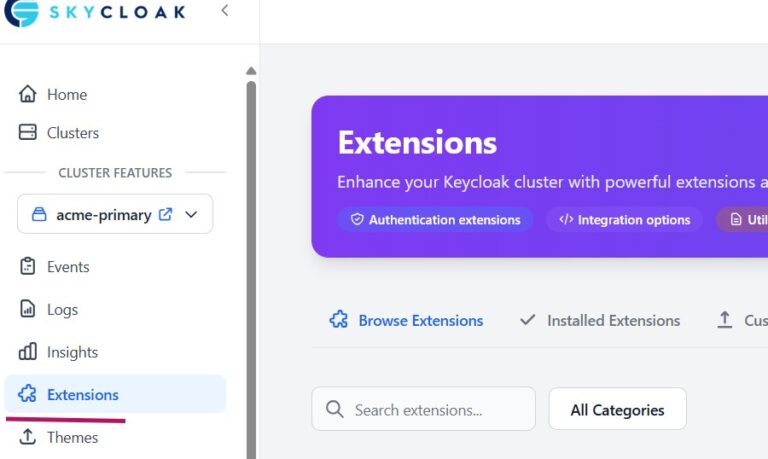
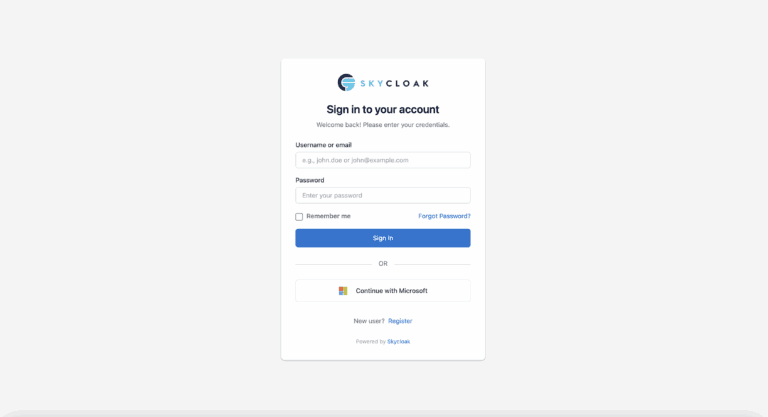
Using Email OTP Keycloak Extension with Skycloak
Learn how to install and configure the email OTP Keycloak extension with Skycloak to add email-based multi-factor authentication to your…

IAM Solutions ROI: Comparing Top Enterprise Options
Compare the true ROI of Auth0, Okta, AWS Cognito, self-hosted Keycloak, and managed Keycloak to find the best enterprise IAM…

Keycloak ABAC Configuration: Step-by-Step Guide
Learn how to configure Attribute-Based Access Control (ABAC) in Keycloak with this step-by-step guide covering policies, resources, and permissions.
Keycloak SAML Security: Common Vulnerabilities and How to Harden Your Configuration
Explore Keycloak SAML security vulnerabilities including CVE-2024-8698, XML wrapping attacks, and assertion replay, with hardening steps.
Setting Up Microsoft Entra ID SSO with Keycloak (OIDC)
Learn how to configure Microsoft Entra ID SSO with Keycloak using OIDC. Step-by-step guide covering app registration, client setup, and…

How Keycloak Secures Node.js Microservices
Learn how to secure Node.js microservices with Keycloak by centralizing authentication, JWT token management, and role-based access control.
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.