keycloak
Articles tagged with keycloak.
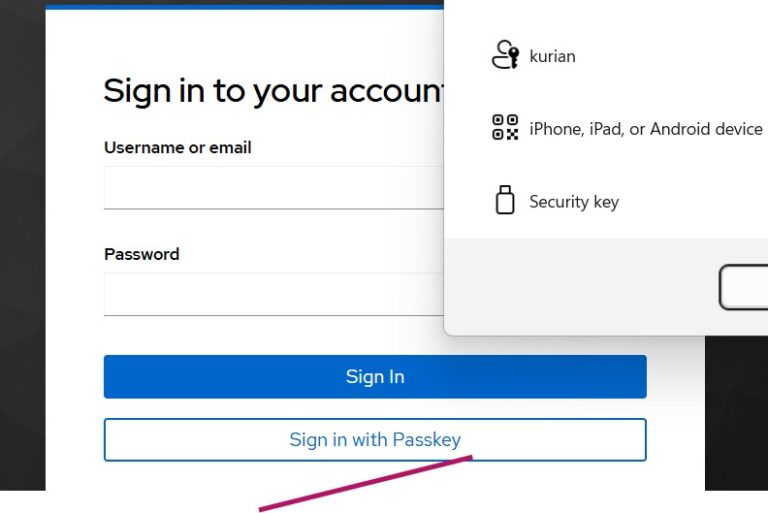
Keycloak WebAuthn Passwordless with Passkeys
Learn how to configure Keycloak for passwordless authentication using WebAuthn passkeys with FIDO2 standards for phishing-resistant login.
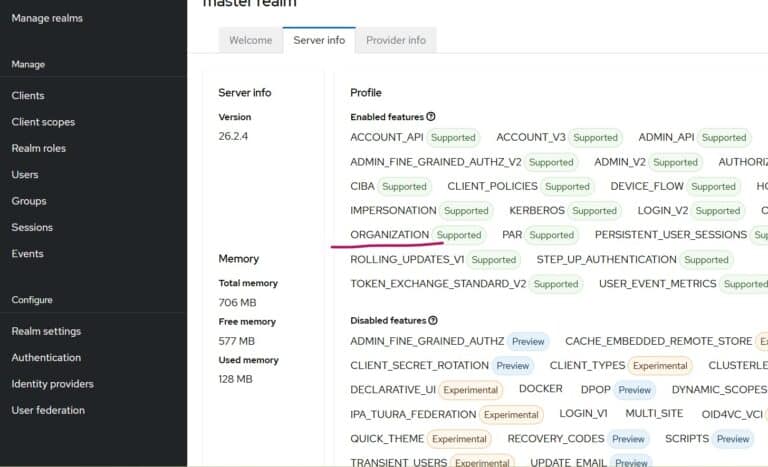
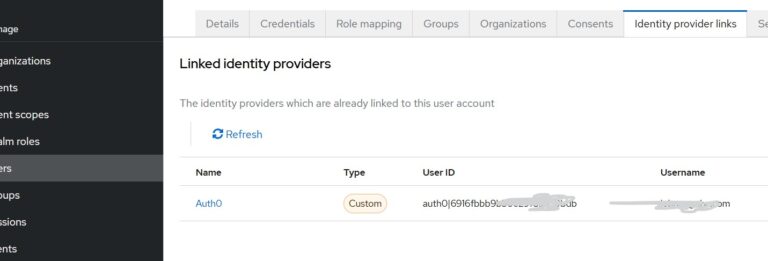
Multitenancy in Keycloak Using the Organizations Feature
Learn how to implement multitenancy in Keycloak using the Organizations feature to link external identity providers and streamline B2B authentication.

Scaling Keycloak: Clustering, Caching, and Load Testing for Production
Learn how to scale Keycloak for production with clustering, Infinispan caching, database optimization, and load testing strategies.

Testing Keycloak: Automated Validation with Testcontainers, Postman, and Cypress
Learn Keycloak testing and automated validation strategies using Testcontainers, Postman, and Cypress to build reliable identity infrastructure.
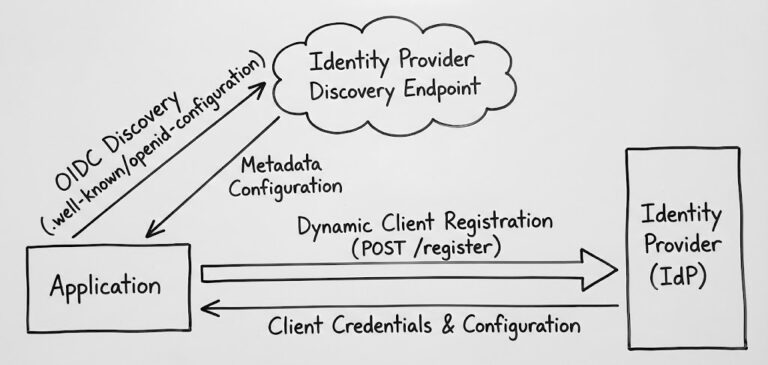
OIDC Discovery and Dynamic Registration: Automating Identity Provider Configuration
Automate identity provider configuration with OIDC Discovery and Dynamic Client Registration to reduce errors, improve security, and scale efficiently.

Session Management in Distributed Systems: Cookies vs Tokens vs Server-Side Sessions
Compare cookies, tokens, and server-side sessions for distributed systems with security analysis, scalability trade-offs, and Keycloak session management.

JWT Token Lifecycle Management: Expiration, Refresh, and Revocation Strategies
Learn JWT token lifecycle management strategies including expiration policies, refresh token rotation, and revocation mechanisms for secure authentication systems.
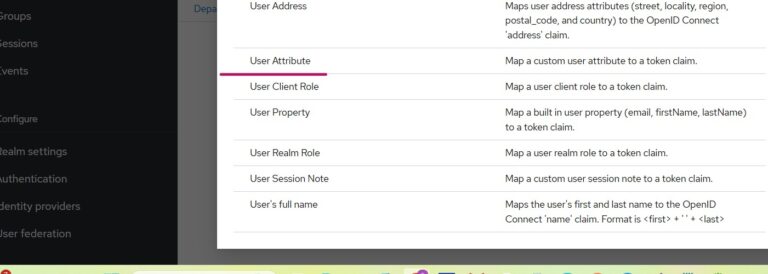
Using Custom User Attributes in Keycloak OIDC Tokens
Learn how to add custom user attributes to Keycloak OIDC tokens and map them to your client application. Includes Spring…
Attribute Mapping in Keycloak During OIDC Identity Brokering
Learn how to map user attributes like email and phone number in Keycloak during OIDC identity brokering with external providers…
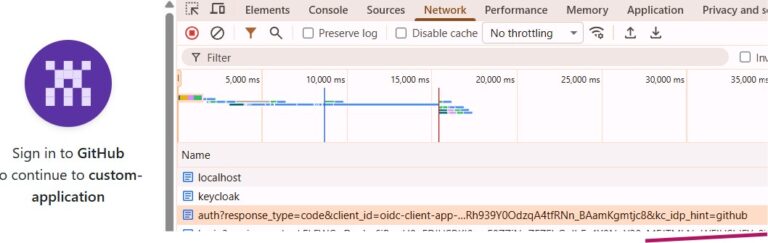
Use kc_idp_hint to Choose Identity Provider in Keycloak
Learn how to use kc_idp_hint in Keycloak to skip the login screen and redirect users directly to a specific identity…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.