Insights on Identity, Security & Keycloak
Tutorials, deep dives, and best practices from the Skycloak team.
Skycloak’s SOC 2 Journey: From Type 1 to Type 2 Certification
Learn how Skycloak achieved SOC 2 Type 2 certification for its managed Keycloak hosting platform, what was audited, and what…
Keycloak Integrations: An Overview for Enterprises
Discover the power of Keycloak integrations in enterprise environments. Learn how to enhance security, streamline authentication, and overcome common challenges…
Is OAuth the Same as SSO? A Beginner’s Guide
Confused about OAuth and SSO? 🤔 You're not alone! Dive into our beginner's guide to demystify these authentication concepts and…
Understanding the Difference Between SSO and SAML
Confused about SSO and SAML? 🤔 You're not alone! Dive into this detailed guide to demystify these authentication concepts and…
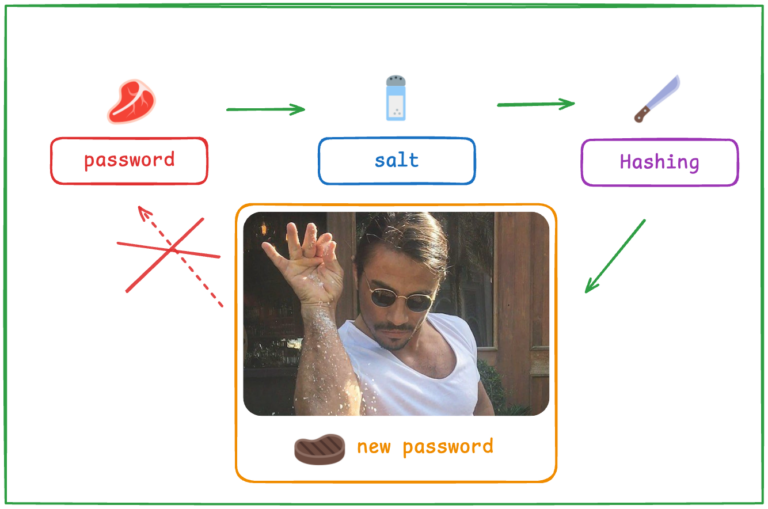
Bcrypt: Why It’s a Preferred Password Hashing Algorithm
Unveil the secrets of bcrypt and learn why it's still a preferred password hashing algorithm. Dive into its basics, real-world…

Device Management in IAM: An Introduction
Unlock the potential of device management in IAM with Keycloak. Learn how to secure devices, address challenges, and implement best…
Exploring Auth0 Alternatives: What’s Right for You?
Looking to move beyond Auth0? Dive into our comprehensive guide on top alternatives, including Keycloak, to find the right fit…
Top Stytch Alternatives for Identity Management
Looking for a Stytch alternative for identity management? Dive into our comprehensive guide comparing top solutions like Keycloak, and find…

How to Prevent Password Cracking in IAM
Is your IAM system vulnerable to password cracking? Unlock the secrets to fortifying your defenses with proven techniques and expert…
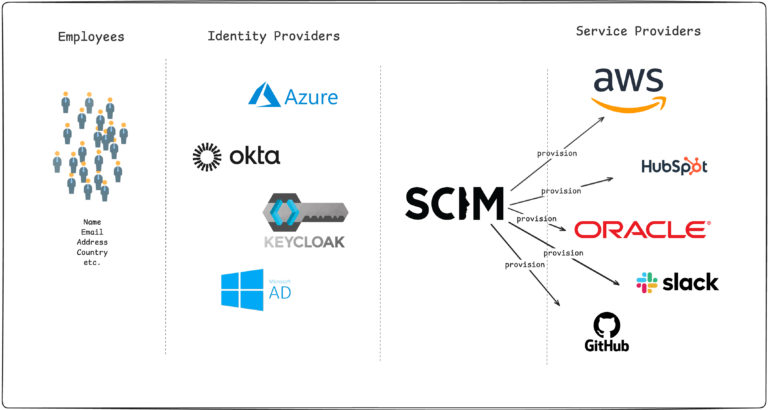
SCIM Protocol: What It Is and Why It Matters
Unlock the secrets of the SCIM protocol and learn how it can transform your user management strategies. Let's dive in!…
Stay ahead on identity & security
Get tutorials, product updates, and Keycloak tips delivered to your inbox.